Hackers Have Had an Easy Way to Install Malware on macOS For Over 10 Years
A group of researchers has today revealed that since 2007, hackers have had an easy way to bypass 3rd-party macOS signature checks by falsely showing them that untrusted apps were signed by Apple. As a result, it has been possible for hackers to pass off malicious code as an app that was signed with the key Apple uses to sign its apps (via ArsTechnica).
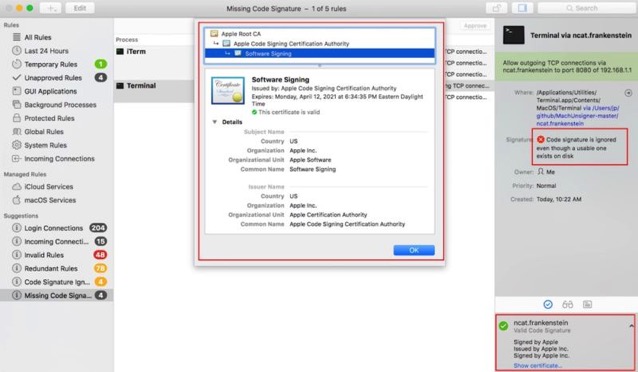
The researchers found at least eight macOS security tools that showed other non-signed executable code included in the same bundle as being signed by Apple too. These tools included VirusTotal, Google Santa, Facebook OSQuery, the Little Snitch Firewall, Yelp, OSXCollector, Carbon Black’s db Response, as well as several tools from Objective-See.
Fortunately though, tools built into macOS weren’t susceptible to the bypass, which has been possible since the release of OS X Leopard in 2007. “To be clear, this is not a vulnerability or bug in Apple’s code… basically just unclear/confusing documentation that led to people using their API incorrectly,” said Patrick Wardle, the developer of the Objective-See tools and Chief Research Officer at Digita Security.
“If a hacker wants to bypass your tool and targets it directly, they will win,” Wardle said. He went on to say that the bypass was the result of ambiguous documentation and comments Apple provided for using publicly available programming interfaces that make the signature checks work.
“Apple updated [its] documents to be more clear, and third-party developers just have to invoke the API with a more comprehensive flag (that was always available).”
To learn more about the technique used to bypass 3rd-party macOS signature checks, click here.