Researcher Says iMessage Security is Not “Impregnable” as FBI Claims
Apple does have a “backdoor” to your iPhones, a security researcher claims in an article published on LawFare. A second security expert speaking with Business Insider has apparently confirmed these claims, saying that Apple probably has the capability to grant the FBI access – at least – to iMessages, which iPhone marketing says are end-to-end secure.
In a lengthy article published on the LawFare blog, Nicholas Weaver, a computer security researcher at the International Computer Science Institute in Berkeley, highlights several methods by which the FBI can access information on or via the iPhone.
First, the IMEI number: This is enough for the FBI to identify the carrier and discover the phone’s entire movement history as long as the phone was on.
But that’s far from accessing content, you say. You’re right. But here are some other scenarios. Secondly, most owners use a weak, 4-digit passcode, which can be easily cracked with a brute-force attack – you can find our earlier reports here on such tools.
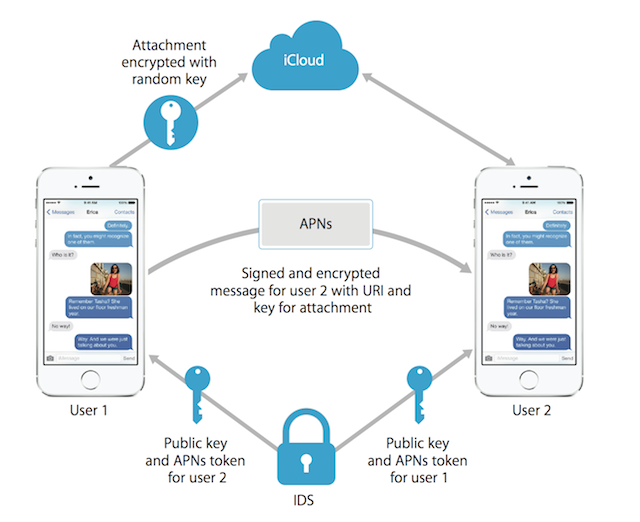
If that’s not enough, you have iMessages. Their weakness lies in its strength: encryption. More precisely, this is how it works. As a first step the FBI can obtain iMessage metadata with a warrant, which means it gets all the information about every message sent and received except the content. But it also gets time information, IP addresses, recipients, and the presence and size of attachments.
But there is more:
When Alice wants to send a message to Bob, Alice’s iPhone contacts Apple’s keyserver, a central authority which knows everyone’s public keys, and asks “I am Alice, please tell me all my public keys” and “I am Alice, please tell me all of Bob’s public keys”. […] But there remains a critical flaw: there is no user interface for Alice to discover (and therefore independently confirm) Bob’s keys. Without this feature, there is no way for Alice to detect that an Apple keyserver gave her a different set of keys for Bob. Without such an interface, iMessage is “backdoor enabled” by design: the keyserver itself provides the backdoor.
Wiretapping an iPhone is pretty straightforward: “Modify the keyserver to present an additional FBI key for Alice to everyone but Alice,” the researcher says. “Now the FBI (but not Apple) can decrypt all iMessages sent to Alice in the future.”
In other words, the FBI is wrong: There are many ways to obtain information from an iPhone. Apple just doesn’t want to “engineer that capability”, F-Secure security advisor Sean Sullivan said regarding the iMessage encryption flaw.