Why Adding Two-Factor Authentication to Find My iPhone is Complicated

Kapil Haresh, a graduate student student at the University of Waterloo studying software engineering with a specialization in cryptography, security, and privacy, posted a piece on Medium detailing what he believes to be limitations in Apple’s two-factor authentication (2FA) implementation. He also released a video of the limitation on YouTube.
He realized that 2FA is not enabled on iCloud’s Find My iPhone feature after he found himself in the middle of such an attack. He discovered that someone was using Apple’s Find My iPhone to ping his device and locked it down by putting it in Lost Mode.
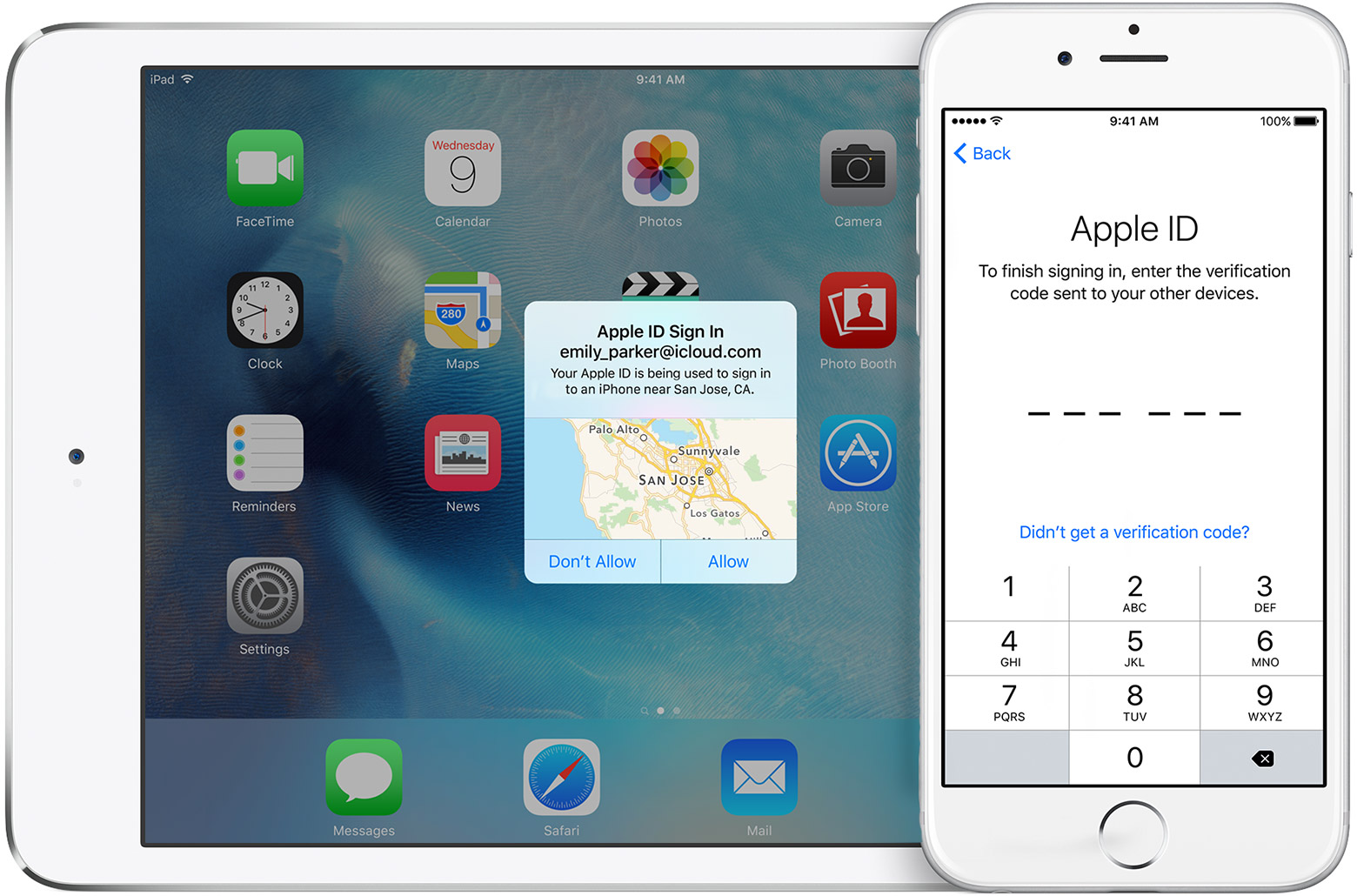
However, Haresh took a very responsible set by turning on 2FA, but he soon realized that 2FA doesn’t cover Find My iPhone, Apple Pay or Apple Watch settings. All of these features appear at the bottom of the screen after entering the username and password. In a statement, he said:
“If Apple doesn’t find a way to restrict Find My Phone to device owners, it will continue to put its users data and privacy in jeopardy.”
Indeed, the lack of 2FA on Find My iPhone can be exploited as a vulnerability but given the nature of the feature, Apple cannot add 2FA to the feature. The reason is because if you lose your iPhone, receiving a 2FA code via SMS on that same iPhone would be completely useless.

Some may argue that you would still be able to get the 2FA code on your iPad or Mac using Apple’s new Continuity feature, which allows users to send and receive SMS messages from their other devices. However, this will not work because Continuity requires your iPhone to be in Bluetooth or Wi-Fi range, which would be impractical in almost all situations. Apple also allows you to send the 2FA code to another phone number, however, there are definitely cases where a user would not have access to another device to send it to.
Others may argue that this is not a valid argument because it gives a hacker too much power to anyone who knows your Apple ID and password. While this argument is valid, a feature like Find My iPhone relies on that convenient access to allow a user to quickly lock or wipe their device if its lost or stolen.
The debate on whether Apple should add 2FA to Find My iPhone is irrelevant. The real debate should be whether or not Apple should add extra security features to Find My iPhone, which cannot be 2FA because that would defeat the purpose of having the feature in the first place.
In his blog post, Haresh mentions Pattern Monitoring as a means to make it more difficult for an attacker to gain access to Find My iPhone. Apple could use location information of the request to detect if the iPhone and the device logged into Find My iPhone are in the same general area (or even city).
I agree that this could definitely work, but if you lose your iPhone in one country and then travel to another before noticing you lost it (say in your baggage at the airport), the legitimate request to wipe the phone or mark it as lost would be invalidated because of Pattern Matching. Of course, Apple would have to look at more than just location. Generally, Pattern Matching could be a part of a bigger solution to the problem, but it does not cover all the edge cases in and of itself.
Haresh then mentions another alternative, which would be to have secret security questions be a second layer of authentication for Find My iPhone. While this would definitely work, most users’ answers to these questions would be easy to guess based on publicly available information on social media sites like Facebook and Twitter. Another problem with this approach from Apple’s standpoint is that by adding security questions and answers there is an additional layer of complexity that makes it harder for the user to achieve their goal of locating their device.
The main argument of Haresh’s post draws us back to two fundamental issues in security. The first being that most attacks can be avoided by using a strong randomized password that you change on a three to six month basis. The second is the argument of convenience vs. security, which has been a challenge for consumer electronic companies, like Apple, for a long time.
I believe that Apple could add some extra security measures to help prevent against these types of attacks, and I think that Apple is already doing a great job of this in their products. Apple is a company that does not want to sacrifice security for convenience or visa versa, so tackling these challenges is especially difficult for them. Google, for example, allows you to print 10 one-time codes that you can use for their two-factor authentication on Android. While printing out codes is no where near the most secure thing you can do, Google is offering a solution to the problem.
When setting up 2FA, Apple provides you with a recovery key which the company could elect to use as a second factor of authentication for Find My iPhone. However, much like Google’s solution to the problem, it’s not convenient and for it to work you must always carry this recovery key with you. Apple is definitely not the company to take a similar approach because its not a convenient solution and its certainly not the most secure.
The idea of having Find My iPhone enabled is to allow you to quickly view the location and take any appropriate action on a lost or stolen device. Adding in extra secondary authentication steps takes away from the very nature of the feature. If you need to quick access to this feature, the last thing you want to happen is to be locked out or be stuck trying to remember answers to your security questions.