LinkedIn iOS App Leaks iCal Data; 6.5M Passwords Reportedly Leaked Too
Another day, and another huge story about an iOS app using your data without you knowing (reminds me of the whole issue with Path). Last night both the New York Times and The Next Web reported your calendar entries are transmitted back to LinkedIn’s servers without your permission or knowledge via the LinkedIn iOS app. The discovery was made by mobile security reseachers Yair Amit and Adi Sharabani, set to detail their findings at Tel Aviv University today.
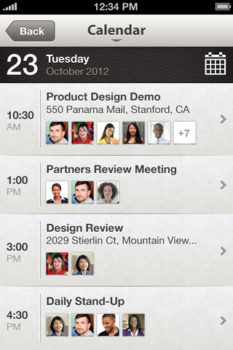
The issue stands with iOS and its opt-in feature that allows users to view their iCal entries within the LinkedIn app. Once users opt-in, LinkedIn automatically sends your calendar data to their servers.
LinkedIn has responded to the calendar ‘leak’ in a blog post, where they clearly state what they do and don’t do with your data:
We Do:
- We ask your permission before accessing your calendar, this will continue to be an opt-in feature
- We provide you with a way to turn off the calendar feature at any time in the settings
- We send calendar data to our server only when the LinkedIn app is launched to be matched with relevant LinkedIn profiles of meeting attendees
- We send your calendar data to our servers over a secure SSL connection
We Don’t:
- We do not store any calendar information on our servers
- We do not share or use your calendar data for purposes other than matching it with relevant LinkedIn profiles
- We do not under any circumstances access your calendar data unless you have explicitly opted in to sync your calendar
We Will Improve:
- We will no longer send data from the meeting notes section of your calendar event
- There will be a new “learn more” link to provide more information about how your calendar data is being used