iOS Flaw Allows Attackers to Log Screen Touches
Just three days after Apple patched an important iOS vulnerability known as “gotofail”, which gave attackers access to sensitive data, iOS researchers have uncovered another flaw; this one allows attackers to log every touch a user makes, including Touch ID presses and volume control adjustments. And yes, this includes logging characters on the virtual keyboard.
Ars Technica points to security firm FireEye’s Monday blog post, which states they have developed a proof-of-concept app that was allowed in the App Store. The uncovered vulnerability affects non-jailbroken iOS 7.0.4, 7.0.5, 7.0.6, and iOS 6.1.x.
We have created a proof-of-concept “monitoring” app on non-jailbroken iOS 7.0.x devices. This “monitoring” app can record all the user touch/press events in the background, including touches on the screen, home button press, volume button press and TouchID press, and then this app can send all user events to any remote server, as shown in Fig.1. Potential attackers can use such information to reconstruct every character the victim inputs. […] Based on the findings, potential attackers can either use phishing to mislead the victim to install a malicious/vulnerable app or exploit another remote vulnerability of some app, and then conduct background monitoring.
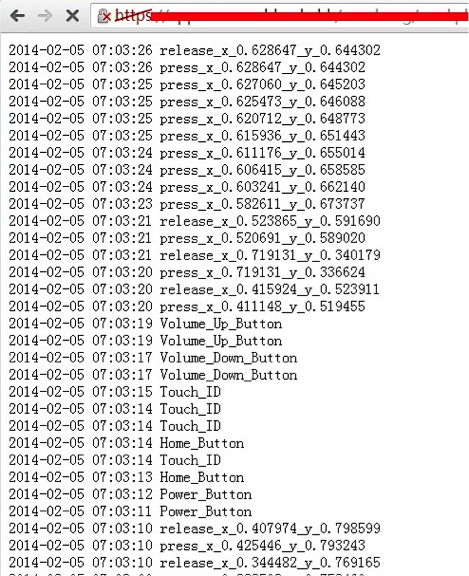
As FireEye points out, the proof-of-concept app uses the built-in multitasking feature of iOS, as it runs in the background and logs every single touch the user inputs. The multitasking feature is used by many apps, such as Music app, Facebook, Skype, etc.
Apple still owes Mac users a security fix for the “gotofail” flaw, and it is poised to release iOS 7.1 shortly, but this vulnerability uncovered by FireEye will perhaps speed up the release. By the way, there is no word about iOS 7.1 being vulnerable, so it could bring the fix we all expect.