iOS Security Bug Allows Hackers to Install Infected App Clones
FireEye has recently spotted 11 iOS apps in the Hacking Team’s arsenal utilising what they call “Masque Attacks”. What this means is that hackers have found a way to get their malicious apps installed on non-jailbroken iOS devices without the user’s knowledge. Such malicious apps are packed in popular messaging and social networking apps such as WhatsApp, Twitter, Facebook, Facebook Messenger, WeChat, Google Chrome, Viber, BlackBerry Messenger, Skype, Telegram, and VK.
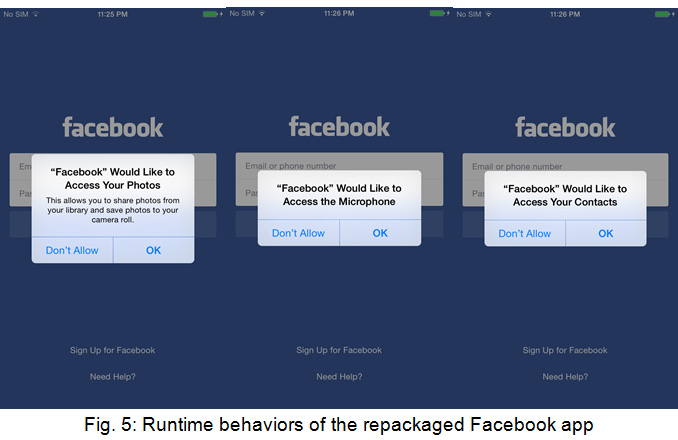
Before you jump to conclusions, these are not the apps you download from the App Store – those are verified, clean apps. What the hackers were able to do is reverse engineer and “weaponize” versions of these popular apps. As FireEye points out, these apps, unlike the genuine versions, come with an extra binary designed to exfiltrate sensitive data and communicate with a remote server. What represents an issue, though, is that these malicious apps can directly replace the genuine apps on iOS devices running versions before 8.1.3.
All this is happening without the user’s knowledge, and the infected versions function just like the genuine apps. The attack works by luring iOS users to click on an infected link while browsing the Web and Masque then downloads the infected app on the iPhone.
In an interview with Business Insider, FireEye global technical lead Simon Mullis explains:
“The most recent version of the Masque attack uses a technique called ‘URL Scheme Hijacking.’ The attacker is initially able to bypass the mechanism used by Apple to ensure that a user trusts an app that is being installed,” he said. “If you can be tricked into clicking on a link on your phone to install an application then any of your apps could be replaced with a malicious version. It could look identical to the standard app but have extra functionality,” Mullis said.
Fortunately, FireEye says, the attacks have affected a small number of victims, without disclosing any numbers. However, Mullis expects such attacks to expand in the near future.
Image credit: FireEye