New Android Vulnerability Lets Apps Record Video Without Permission
A new bug discovered in the Android Camera app affecting millions of devices lets third-party apps record video, take pictures, and even extract GPS data from media to get a device’s location without requiring the user’s permission (via Bleeping Computer).
The vulnerability has been disclosed by researchers from Checkmarx in a coordinated disclosure with Google and Samsung. Called CVE-2019-2234, the bug affects the Google Camera and Samsung Camera apps if they have not been updated since before July 2019.
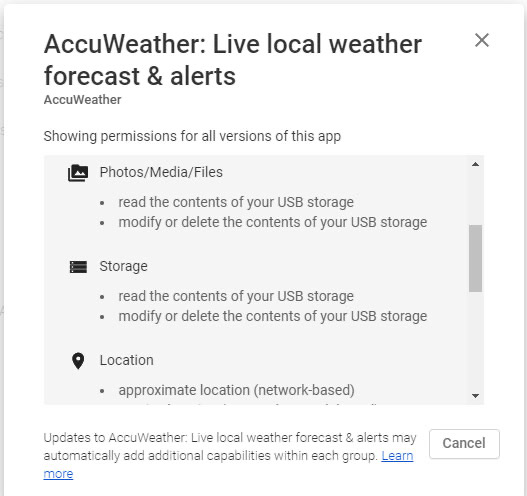
The researchers found that apps that have the ‘Storage’ permission to access the device’s entire SD card and the media stored on it also gives an app the ability to use the Camera app’s exposed intents to take pictures and record video.
“A malicious app running on an Android smartphone that can read the SD card, not only has access to past photos and videos, but with this new attack methodology, can be directed to initiate (take) new photos and videos at will. And it doesn’t stop there. Since GPS metadata is usually embedded into the photos, the attacker can take advantage of this fact to also locate the user by taking a photo or video and parsing the proper EXIF data. “
Google says the vulnerability in the Camera app was fixed in July 2019 via a Google Play Store update and a patch was issued to other vendors.
Below is a proof-of-concept video showing a weather app quietly sending a picture, video, and phone call recordings back to a remote server.