Apple Statement on ‘Masque Attack’: OS X and iOS Have Built-In Safeguards
Apple has released a statement on ‘Masque Attack’, which appeared to get more headlines today as the U.S. government posted a public warning about hackers tricking iOS Enterprise Developer and developers into installing fake apps posed as malware, which could then steal sensitive data.
In a statement to iMore, Apple reminded users both OS X and iOS have built-in security safeguards to protect you–and that they have not heard of customers affected by this attack yet:
“We designed OS X and iOS with built-in security safeguards to help protect customers and warn them before installing potentially malicious software,” an Apple spokesperson told iMore. “We’re not aware of any customers that have actually been affected by this attack. We encourage customers to only download from trusted sources like the App Store and to pay attention to any warnings as they download apps. Enterprise users installing custom apps should install apps from their company’s secure website.”
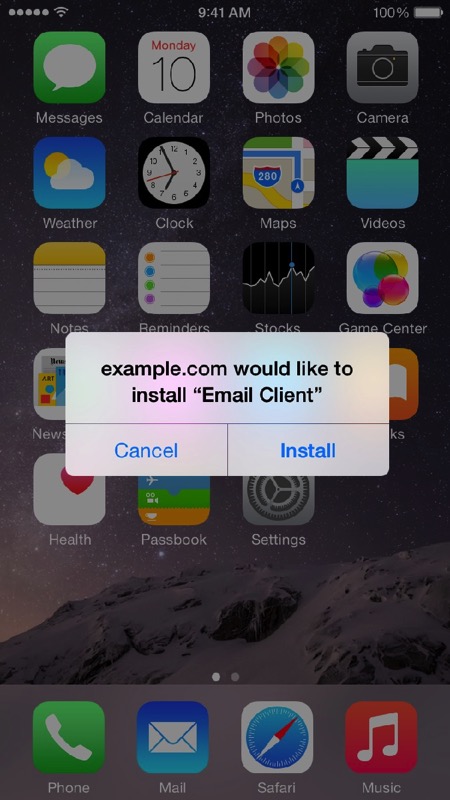
Apple says as long as you are downloading apps from the App Store and trusted custom enterprise apps from your company’s website, you’ll be safe. An updated support document details examples of what to expect when you see trusted and untrusted sources of app installations.
This is what you’d expect to see when you’re downloading an app from your trusted company’s website:
This is an example of a warning iOS will display if an app is from an “Untrusted App Developer”. This is when users are supposed to think and tap “Don’t Trust” and then delete the app:
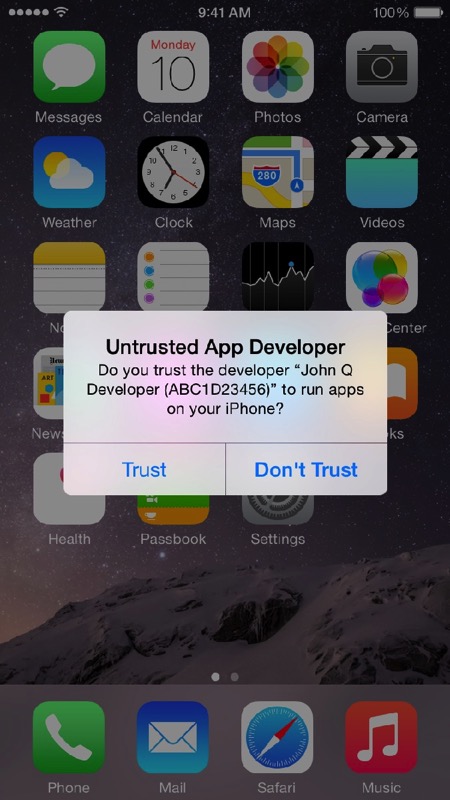
If you’re able to follow these simple guidelines, your iOS device will remain safe.