Famous iPhone Hacker ‘Geohot’ Demos a Simple Computer Hack
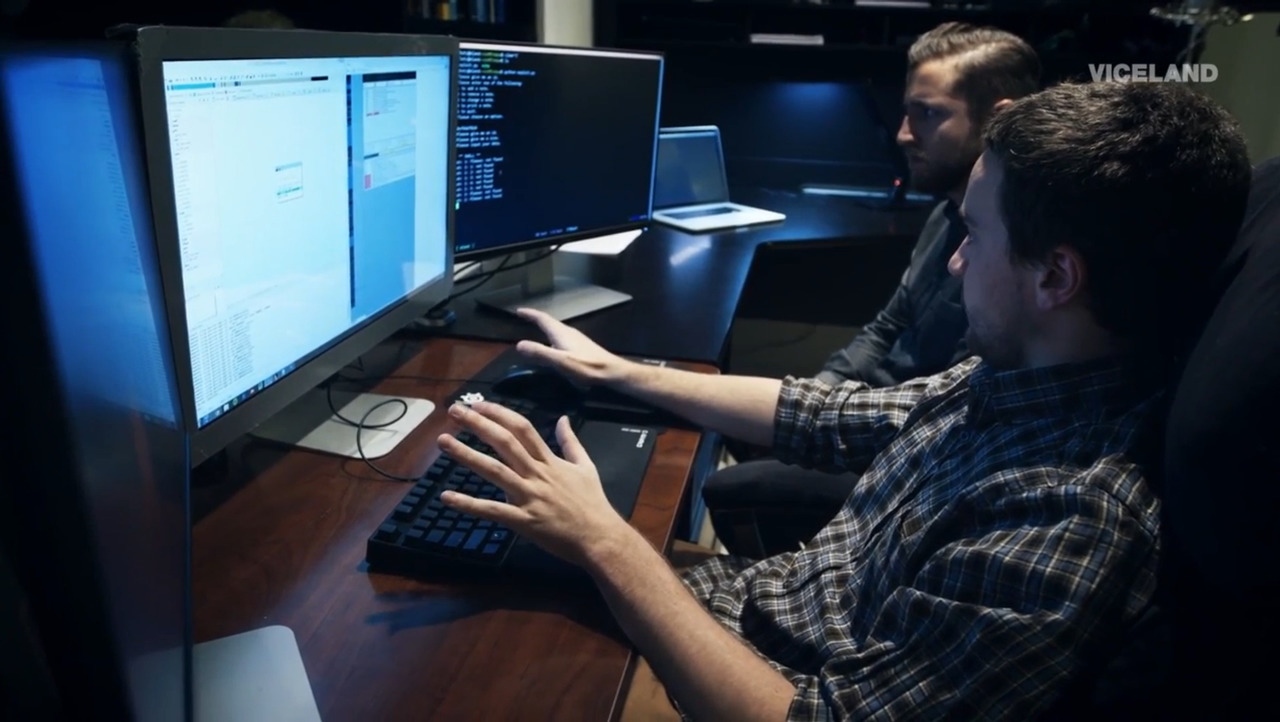
George Hotz, the hacker known for unlocking the iPhone, rooting the PS3, and developing technology for self driving vehicles, has demonstrated a simple hack in a video produced by Viceland.
The video shows Hotz walking and talking through the necessary steps involved in gaining access to a laptop connected to a Wi-Fi network. That laptop also has a vulnerable piece of software installed on it to allow the demonstration to take place. The video does not go into any intricate details, but it does give a good insight into the mindset of a hacker.
The process of finding out what vulnerable software a machine is running, examining the vulnerability, and then building a program that bundles in an exploit to hack that machine is extremely technical.
In the example shown in the video, Hotz managed to exploit a vulnerable software on the Wi-Fi connected laptop with just 65 lines of Python code. For those interested, the exploit written by Hotz takes advantage of a buffer overflow in the software running on the laptop.
A buffer overflow occurs when a program tries to story more data in a buffer (a temporary data storage area in memory) than it was intended to hold. Since a buffer can only hold a finite amount of data, the extra information, which has to go somewhere, can overflow into the adjacent buffers. This can corrupt or overwrite the valid data held in that other buffer. Although a buffer overflow can occur accidentally though a programming error, buffer overflow attacks is an increasingly common type of security attack on data integrity.
In buffer overflow attacks, the extra data may contain codes designed to trigger specific actions, in effect sending new instructions to the attacked computer. These instructions could damage the user’s files, change data, or disclose confidential information.
Finding the vulnerability allowed Hotz to gain shell access to the laptop, which means that he can run almost any command from a terminal session. I say almost because certain commands will require root access to the machine, which may require extra work to get depending on how the user’s profile is configured. As shown in the video, this can include opening apps and browsing files of the victims machine. With shell access, Hotz can do a lot more damage to the victims machine, including viewing, deleting, and retrieving copies of the user’s data.
Hotz also mentions the ability to keep a persistent connection with the victims laptop, which means that even after a reboot the hacker would still have access to the machine. An attacker who gains shell access would also be able to execute commands without the user knowing, as there would be no visible sign of activity.
Check out the full video of the hacking session with Geohot below:
[via TechInsider]