
iOS App Vulnerability Gives Hackers Access To Data Over WiFi [VIDEO]
According to a group of mobile security researchers, they have discovered a new vulnerability in iOS apps that use WiFi, that can give a hacker access to the information being provided to the mobile device when used over an unsecured WiFi network, The New York Times is reporting. The researchers, who belong to mobile security company Skycure, claim that they had alerted app makers in the past about this vulnerability, before making it public.
Yair Amit, Skycure’s chief technology officer said, “The vulnerability affects so many apps that it’s virtually impossible to alert app makers”. The researchers added that the vulnerability was present in hundreds of apps they tested, including stock management and news apps. They declined to name the apps affected for fear attackers would use the knowledge and exploit it. The source reports that following disclosure, LinkedIn tweaked its code to stop taking notes from private calendar appointments.
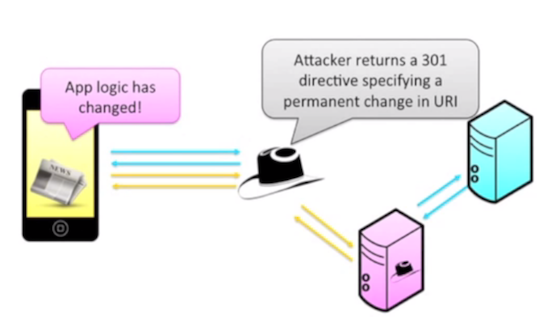
“The vulnerability allows attackers to persistently alter the server URL from which a mobile app loads its data, so that instead of loading data from realserver.com, for instance, the attack makes the app load data from attacker.com, without the victim knowing. Attackers could use that data to load malicious links, or insert fake, market-moving news into a news app”.
The researchers have put together a short video demonstrating how attackers can manipulate an app. They use what is called a 301 directive to redirect the traffic flow from an app to an app maker’s server to the attackers’ server. Take a look:


