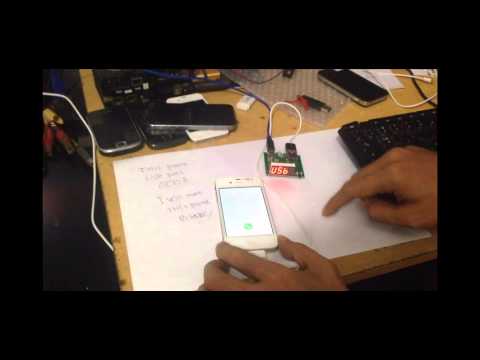
Hardware Device ‘IP Box’ Breaks iPhone Passcodes Using Brute Force [VIDEO]
IP-Box is a new black box that is able to guess your iPhone’s four-digit PIN using an exploit patched by Apple with iOS 8.1.1. Identified as CVE-2014-4451, iOS had a flaw allowing an attacker in possession of a device to exceed the maximum number of failed passcode attempts.

The black box was brought into the spotlight by MDSec (via Daring Fireball). The guys weren’t sure whether this was related to the aforementioned flaw, but the documentation posted on the Internet clearly points to this security flaw iOS had — until Apple patched it.
So what exactly does IP-Box do? Well, shortly put, it does an apparently simply job: “it simulates the PIN entry over a USB connection and sequentially bruteforces every possible PIN combination,” the MDSec blog post states.
Basically, IP-Box operates by sending predefined passcode lists to the targeted iOS device. Each attempt takes approximately 6 seconds to perform, and so the dictionary containing all numbers between 0000 and 9999 would take between 6 seconds and approximately 17 hours to complete.
One of the sites detailing IP-Box’s capabilities warns users to that if the iOS device has the “Erase Data After 10 Failed Passcode Attempts ” feature activated, the device would be wiped after IP-Box reaches 10 password attempts. However, the guys from MDSec were able to cleverly bypass this security feature of iOS by “connecting directly to the iPhone’s power source and aggressively cutting the power after each failed PIN attempt but before the attempt had been synchronized to flash memory.” Brilliant move.
Update: This exploit only targets devices running iOS 8.1 or lower with 4-digit passcodes. You can protect yourself by upgrading to iOS 8.2 and by using a complex passcode (not a 4-digit PIN).
You can watch IP-Box in action in the videos inserted below: