iPhone Exploited at CanSecWest: Browser Jailbreak Revived?
Earlier this week we setup a poll asking which smartphone would be the first to fall at the 2010 CanSecWest conference currently held in Vancouver. With the security competition started, the iPhone was one of the first to fall through a mobile Safari-based exploit.
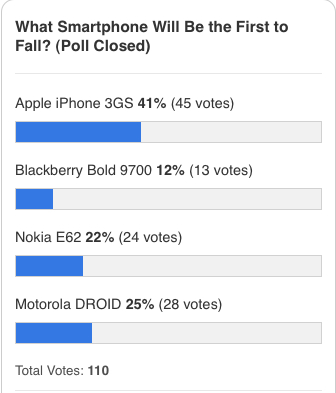
Our poll resulted in the following after over 100 votes:
Here’s what happened during the iPhone portion of the contest according to CNET:
For the iPhone contest, Iozzo and Weinmann wrote an exploit in about two weeks that was designed to steal the contents of the SMS database on an iPhone.
To accomplish the attack the target iPhone was used to visit a Web site hosting exploit code. “The payload executes and uploads the local SMS database of the phone to the server we control,” said Weinmann.
The exploit was written to bypass the digital code signatures used on the iPhone to verify that the code in memory is from Apple, he said. The exploit then looked for chunks in Apple’s code that could be pieced together to accomplish the attack, according to Weinmann.
“Bypassing the code signing was a major issue,” Flake said. The technique used has been known since 1997 but has not been used on an ARM processor until now, he added.
MuscleNerd Confirms This Could Reincarnate the Safari-Based Jailbreak!
Remember when your iPhone 2G could be jailbroken by visiting jailbreakme.com in Safari (that seemed like a LONG time ago!)? That was by far the easiest jailbreak of all time! This latest browser exploit could bring back the good ‘ol days according to MuscleNerd of the iPhone Dev Team, via twitter:
Congrats to @_snagg and @esizkur. This potentially re-opens userland jailbreaks that haven’t been around since 1.x days (jailbreakme.com)
MuscleNerd goes on to warn that Apple will surely close this loophole, and that future jailbreakers should avoid all firmware updates! You’ve been warned (over and over and over and over…)!
Who remembers visiting jailbreakme.com? That was an amazing 1.1.1 jailbreak, since earlier jailbreaks required much more courage and risk-taking!
[CNET]