This Vulnerability Can Render an Android Phone Apparently Dead
Trend Micro has today discovered a new vulnerability in Android that can render a phone apparently dead i.e silent, unable to make calls, with a lifeless screen. The security firm notes that the vulnerability is present from Android 4.3 (Jelly Bean) up to the current version, Android 5.1.1 (Lollipop), which means it is present in over 50% of Android devices in use today.
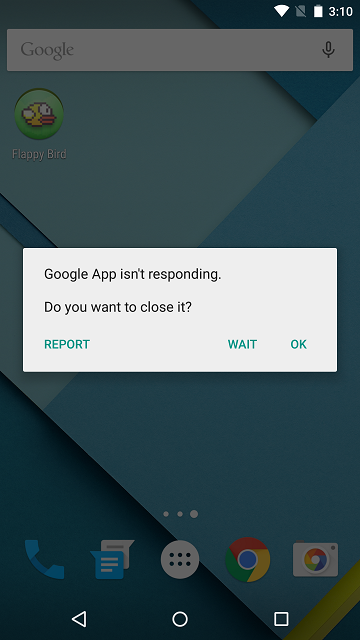
According to Trend Micro, no patch has yet been issued in the Android Open Source Project (AOSP) code by the Android Engineering Team to fix this vulnerability, which can be exploited either via a malicious app installed on the device, or through a specially-crafted web site. The security report details that the first technique can cause long-term effects to the device i.e. an app with an embedded MKV file that registers itself to auto-start whenever the device boots would case the OS to crash every time it is turned on.
“The vulnerability lies in the mediaserver service, which is used by Android to index media files that are located on the Android device. This service cannot correctly process a malformed video file using the Matroska container (usually with the .mkv extension). When the process opens a malformed MKV file, the service may crash (and with it, the rest of the operating system).
The vulnerability is caused by an integer overflow when the mediaserver service parses an MKV file. It reads memory out of buffer or writes data to NULL address when parsing audio data.”
For source code and a proof-of-concept app for the vulnerability, take a look at the source article.