
Apple Gatekeeper Vulnerability Not Fixed Yet: Researcher
Despite shipping a patch, Apple has failed to fix the core of the Gatekeeper vulnerability originally reported last September, the security researcher who originally discovered the security bug has told Ars Technica.
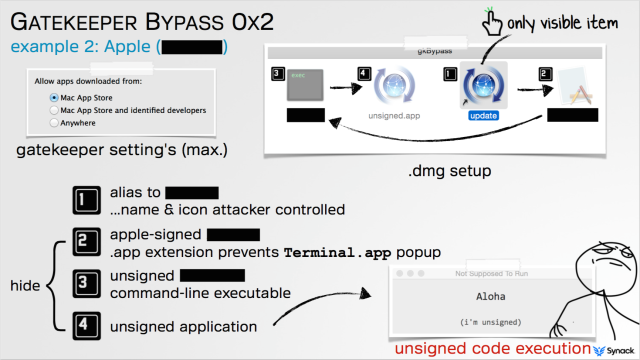
What Apple has done instead is a temporary workaround: It blacklisted the small number of known files the security researcher reported. This isn’t enough, suggests Patrick Wardle, director of research at security firm Synack.
He was able to bypass OS X’s security by using a new Apple-trusted file offered by security firm Kaspersky Lab. Apple released an update to also block that file, earlier on Thursday. But the problem doesn’t stop here. What Wardle tried to highlight is that Apple is currently offering a workaround, not fixing the core of the problem.
“It literally took me five minutes to fully bypass it,” Wardle, who is director of research of security firm Synack, told Ars, referring to the updated Gatekeeper. “So yes, it means that the immediate issue is mitigated and cannot be abused anymore. However the core issue is not fixed so if anybody finds another app that can be abused we are back to square one (full gatekeeper bypass).”
Speaking with Wardle, an Apple representative said the new files he reported have been blocked, that they are aware of his research, and that they are continuing to “work on ways to make Gatekeeper more effective.”

