
Pod2g Discovers iPhone SMS Spoofing Exploit That Has Existed Since 2007 [Update]
In a blog post published in the early morning, iOS security researcher which we have all known as pod2g noted he had come across a ‘severe’ SMS spoofing exploit on the iPhone:
I mentioned it on twitter a few days ago, I found a flaw in iOS that I consider to be severe, while it does not involve code execution. I am pretty confident that other security researchers already know about this hole, and I fear some pirates as well.
The flaw exists since the beginning of the implementation of SMS in the iPhone, and is still there in iOS 6 beta 4. Apple: please fix before the final release.
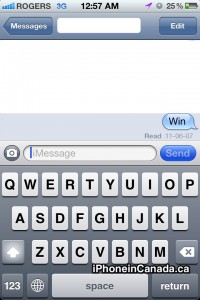
In plain English, the exploit allows someone to send you a text message but change the reply-to address of the text. So you could receive a text message from someone you trust, but it could be illegitimate. Here’s how it’s different on the iPhone:
On iPhone, when you see the message, it seems to come from the reply-to number, and you [lose] track of the origin.
Pod2g notes the following reasons why we should be worried about this exploit and to never trust the SMS messages we receive on our iPhones:
- pirates could send a message that seems to come from the bank of the receiver asking for some private information, or inviting them to go to a dedicated website. [Phishing]
- one could send a spoofed message to your device and use it as a false evidence.
- anything you can imagine that could be utilized to manipulate people, letting them trust somebody or some organization texted them.
Of course, if you question random text messages claiming to come from ‘your bank’ asking for your credit card number and expiry, you should be okay. But its the people who would believe these texts that need to be worried. I’m surprised this exploit has been available for so long, but kudos to pod2g for making it public and encouraging Apple to fix this.
Note to self: never believe any text messages I receive from this day on, ever again.
Update: Pod2g has posted an update and noted you can now verify his earlier claims via his release of sendrawpdu:
The little tool sendrawpdu, based on iphone-elite’s sendmodem is now on github.With an iPhone 4, and this sample code, you can verify my statements for free 😉 .
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


We have 3 iPhones on a Rogers family plan and we all received texts from different numbers within 20 minutes of eachother asking us to click on this link to “claim our free tickets to a cruise”
You have to be quite out of the loop to tap on a link like that
LOL. Yeah I know. Some people like to believe stuff like that though, just ask any prince in Nigeria.