
Hacker’s iOS Developer Account Shut Down After Malware Uploaded to App Store
In a story documented by Forbes, hacker Charlie Miller was able to upload a malware-infested app into the App Store:
At the SysCan conference in Taiwan next week, Miller plans to present a method that exploits a flaw in Apple’s restrictions on code signing on iOS devices, the security measure that allows only Apple-approved commands to run in an iPhone or iPad’s memory. Using his method–and Miller has already planted a sleeper app in Apple’s App Store to demonstrate the trick–an app can phone home to a remote computer that downloads new unapproved commands onto the device and executes them at will, including stealing the user’s photos, reading contacts, making the phone vibrate or play sounds, or otherwise repurposing normal iOS app functions for malicious ends
Video below:
Since his discovery of this major exploit in iOS, Apple has shut down Miller’s developer account and pulled his approved app from the App Store.
A former NSA analyst, Miller is one of the most highly skilled iPhone hackers, and has a knack for exploiting the device. Just this spring, he won the Pwn2Own conference here in Vancouver for a third year in a row for ‘pwning’ an iPhone 4 faster than anyone else.
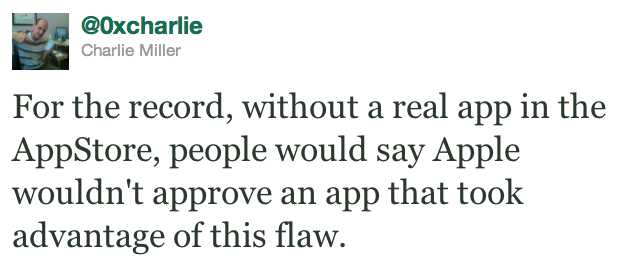
Miller just noted the following on twitter:
For the record, without a real app in the AppStore, people would say Apple wouldn’t approve an app that took advantage of this flaw.
Apple will most likely close this exploit when iOS 5.0.1 is released in a few weeks to address battery life issues. I’m not surprised Apple would pull his account, as he violated the terms of the developer account. Yet at the same time, he helped Apple address a massive security hole in iOS. I guess we can say Charlie ‘took one for the team’, eh?
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


There are better ways to show that you found an exploit that don’t take an antagonistic posture. HE could have done a lot more by working with Apple, and he “has a sleeper app” so that he can prove his point. That is just plain bull and shows the lack cooperation. It also shows that he only thinks of himself, not of the whole.
Don’t be a dumb ass. If “he only thinks of himself”, he wouldn’t of made this exploit public. He obviously wanted to demonstrate just how vulnerable iOS really is on his own terms, not Apples.
Kinda surprising that it took somebody this long to discover this.
Try yourself. Tc***@***le.com
There used to be better ways of talking to Apple and reporting bugs, NO MORE. Has anyone tried recently to email one of the boys at Apple? Remember the time Steve Jobs and Tim Cook answered all emails “Sent from my iPhone”? Well, that’s no more. After Steve’s passing, I’ve tried a few emails including Tim Cook’s to bring up a few very important issues to their attention (as an experienced consultant I wanted to report a few serious things) and no reply!! Non at all, not even “we got your email, now buzz off”. I guess it was just a matter of time. They were waiting for poor Steve to die and now, they can pay bonuses to themselves out of Steve’s dreams and hard work before they destroy what he built so well. Pity.