
Janicab.A Malware Uses Right-To-Left Override Trick to Compromise the Mac OS X System
After a long period of silence, Webroot, F-Secure and Avast have uncovered a new malware that equally targets Mac OS X and Windows (via Ars Technica). Janicab.A is an unusual trojan; the malware developers have found an interesting method to compromise the Mac OS X system.
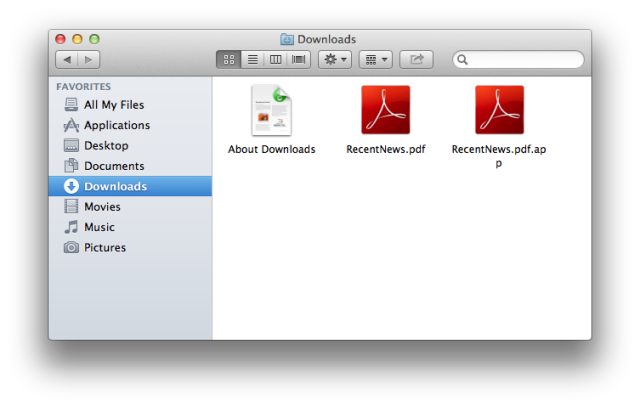
As the Webroot blog points out, the Janicab.A malware was signed with a valid Apple Developer ID, and employing something called “right-to-left encoding,” using the built-in Mac OS X Character Viewer.
Webroot explains how it works:
As a part of the built-in Mac OSX Gatekeeper malware security, when a user attempts to open an .app package that has been downloaded from the internet, the OS alerts the user with a warning asking the user if they would like to continue with the .app installation. In this case however, since the .app package has been renamed using the Unicode right-to-left character encoding, the OS will display the typical warning message written completely backwards, which becomes very confusing to the user, since they can’t understand what is being asked of them. The malware author of course hopes that in the confusion, the user will simply click “open” and continue with the installation. In addition to the OSX warning message, Apple’s Gatekeeper has an additional setting that allows users to choose to only install .app packages that are signed with a valid Apple Developer ID. In the case of OSX.Janicab.A, the malicious .app package is actually signed with a legit Apple Developer ID. Although this does allow the malware author to meet the requirement of a signed .app, it also does allow Apple to easily stop this type of malware distribution in its tracks by revoking the developer account.
As soon as the user allowed the installation of the disguised .app package, the Janicab.A trojan gets to work: it connects to various malicious URLs to obtain the address of its command and control server. After this step completes, the malware takes screenshots, records audio, and uploads them to a remote server.
The Janicab.A comes after Apple has patched several Java-vulnerabilities earlier this year and fought against an adware trojan Yontoo, in March.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


might have to actually get an anti-malware program for my Mac. Weird. Actually so few and far between I might not bother since it will probably get patched.