Newly Discovered Bug Makes iOS Devices Vulnerable to Remote Cyberattacks
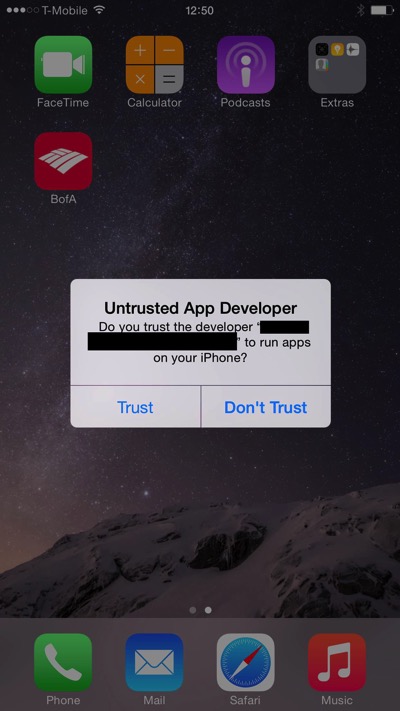
According to a report by Reuters, cybersecurity firm FireEye have uncovered a new bug in iOS that makes most iPhones, iPods and iPads vulnerable to remote cyberattacks. Researchers say that an iOS app installed using enterprise provisioning could replace another genuine app installed through the App Store, as long as both apps used the same ‘bundle identifier’.
“This in-house app may display an arbitrary title (like “New Flappy Bird”) that lures the user to install it, but the app can replace another genuine app after installation. All apps can be replaced except iOS preinstalled apps, such as Mobile Safari. This vulnerability exists because iOS doesn’t enforce matching certificates for apps with the same bundle identifier. We verified this vulnerability on iOS 7.1.1, 7.1.2, 8.0, 8.1 and 8.1.1 beta, for both jailbroken and non-jailbroken devices. An attacker can leverage this vulnerability both through wireless networks and USB. We named this attack ‘Masque Attack’.”
The security firm notes that they notified Apple about the Masque Attack vulnerability back in July. However, recently discovered “WireLurker” malware is found to utilize a limited form of Masque Attacks to attack iOS devices through USB. Since Apple has not yet addressed the issue, they say that they consider it urgent to let the public know, as Masque Attacks can pose much bigger threats than WireLurker.
It appears that Masque Attacks can also replace authentic apps, such as banking and email apps, using attacker’s malware through the Internet. This means the attacker can steal user’s banking credentials by replacing an authentic banking app with an malware that has identical UI.
It must be noted that Masque Attack can happen completely over the wireless network, without relying on connecting the device to a computer. Below is a link to a demo video that shows Masque Attack in action.