
Inside the FBI Encryption War vs Apple: A Careful Legal Battle Planned Months Ago
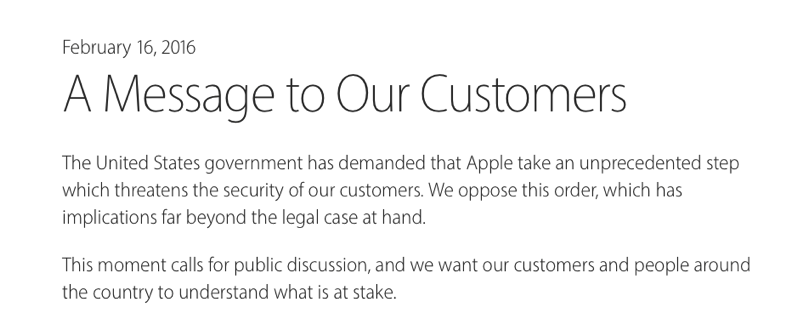
Apple was ordered by a US federal court to develop software that would allow the FBI to hack the iPhone 5c used by San Bernardino gunman Syed Farook. Instead of complying with the order, Apple posted a public letter signed by Tim Cook in which he explains that this single case could create a precedent and that the implications go beyond unlocking a single iPhone, so it won’t comply with the order. Macworld and the Guardian give more insight into why and how the battle started, and where it is heading.
First of all, there are three important aspects users should keep in mind while reading the reports:
– Apple is being asked to create new software to hack its own security system.
– The FBI is using an emotional, infamous terrorism case to publicly justify its request.
– The FBI’s request refers to the All Writs Act, which has already been used once in a case involving an iPhone 5s.
As detailed by Dan Guido at Trail of Bits, here is the technical road block the FBI has faced while trying to access the locked content on the iPhone, as cited by Macworld:
As many jailbreakers are familiar, firmware can be loaded via Device Firmware Upgrade (DFU) Mode. Once an iPhone enters DFU mode, it will accept a new firmware image over a USB cable. Before any firmware image is loaded by an iPhone, the device first checks whether the firmware has a valid signature from Apple. This signature check is why the FBI cannot load new software onto an iPhone on their own—the FBI does not have the secret keys that Apple uses to sign firmware.
While most agree that the FBI should stop the kind of evil that happened in San Bernardino, there is a problem here: If Apple assists in this case, it is likely to receive a flood of similar law enforcement requests.
Here is what Julian Sanches, a surveillance law expert at the libertarian-leaning Cato Institute in Washington, told the Guardian:
“The law operates on precedent, so the fundamental question here isn’t whether the FBI gets access to this particular phone. It’s whether a catch-all law from 1789 can be used to effectively conscript technology companies into producing hacking tools and spyware for the government.”
Apple and the government, observers and people close to the case said, want to set a legal precedent about where digital security ends and national security begins after nearly two years of hearings, open letters and Washington-Silicon Valley shadowboxing. Speculation has already begun about how far both sides are willing to go in appealing unfavorable rulings.
It turns out that the FBI has been preparing its legal battle for months, according to US officials and tech executives speaking with the Guardian. The reason: Apple and the government are battling over whether “national security can dictate how Silicon Valley writes computer code.”
You may recall the outrage (from the FBI) when Apple introduced enhanced encryption in 2014. Since then, the FBI has been trying to figure out a way to force Apple to comply with its demand: Give up and grant access to the software.
“This wasn’t a fluke they picked this one,” said James Lewis, a cybersecurity expert at the Center for Strategic and International Studies who advises technology companies and the government on encryption. “They’re always strategic in how they do these things.”
The San Bernardino case came up just in time. You may recall that iPhones have an optional feature that will erase all the data on the phone if the passcode is entered incorrectly 10 times. The FBI didn’t take the risk but instead came up with a clever request: Don’t turn off encryption, just make it easier for law enforcement agencies to guess the password as many times as they want.
So finally, what are the implications? If Apple does create the software to hack its own customers, this could work even on newer devices with the enhanced encryption of Secure Enclave, the company says.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


Istvan….All “WRITS’ Act
Thanks man!
When you really start to think about it. Agencies like the NSA and CIA really need two things. A: Access to the device and B: The public perception that the device cannot be accessed even by them.
Wouldn’t it be something if some smart people in the government has already found a flaw to exploit and has gained access. Now they just need to convince everybody to keep using their trusted devices.
Remember: “Only the paranoid survive.”
Hope Apple stands strong on this issue. As the article says this is an important precedent. Unfortunately, this generation has a history of giving up its rights in favour of some vague promise of more ‘safety’.