iPhone 4S and Galaxy S3 Are Exploited At The Mobile Pwn2Own Competition
Earlier today at the Mobile Pwn2Own competition, the iPhone 4S and Galaxy S3 were proven insecure as exploiters demonstrated their hacking abilities in Amsterdam. Starting off with the iPhone 4S, here is how Dutch security researchers completed the hack:
iPhone 4S
Dutch security researchers were able to form a webkit browser exploit within a matter of weeks. A code is secretly placed within the background of a website’s coding. With that, all security boundaries of Safari are bypassed and the webpage can send a user’s contacts, pictures, and other similar data to the hacker.
According to security researchers, Joost Pol and Daan Keuper, the attack is compatible with iOS 5.1.1, iOS 6 beta, and feasibly the final release of iOS 6. The exploit earned the duo $30,000 and few other unnamed prizes.
But don’t worry, they aren’t selling the exploit off, it’s to be handed to Apple: (via Computerworld)
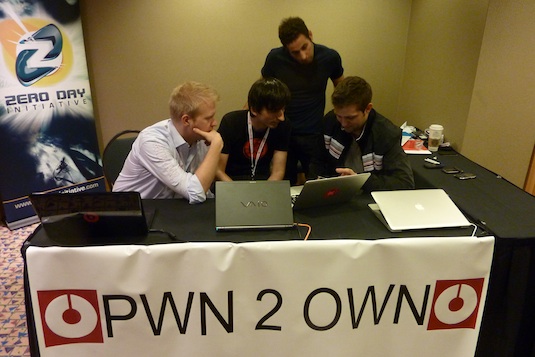
“Any browser exploit is significant,” said Brian Gorenc, manager of the Zero Day Initiative (ZDI) of HP DVLabs, which organized the competition. But because it is another hole in WebKit he does not think that Apple is to blame. He too, however, stressed that this is a hole that should be fixed. “The guys did a great job,” he said, adding that the exploit will be sent to Apple.
Galaxy S3
Researchers at security company MWR Labs showcased their NFC exploit to the public. As we know, Galaxy S3 users can complete a file transfer using NFC when holding the phones near each other. Here is how the system was exploited: (via CIO)
Using this technique, a file is loaded on the targeted S3. The file is then automatically opened and gets full permissions, meaning that the attacker has full control over the phone, explained Tyrone Erasmus, security researcher at MWR. The app runs in the background so the victim is unaware of the attack, he added.
With full access, the receiving end is capable of viewing contacts, emails, pictures, SMS messages, and more. Pwn2Own organizer Dragos Ruiu said the exploit was so powerful that “they demonstrated full ownage of the phone.” Most exploits presented at the event were aimed at a specific part of a phone.
The security researchers received $30,000 and other prizes just like the iPhone 4S team.
Well, that just comes to show that smartphones are very much vulnerable to hackers. Many exploits presented at the event were said to be developed within 2 to 3 weeks of part-time work.