
Google Catches Russian-Backed Group’s Malware Disguised as Pro-Ukraine App
Google’s researchers have just discovered malware from a Russian state-backed group disguised as a pro-Ukraine app. The app had to be manually installed from the APK file rather than being hosted on Google Play, The Verge reports.

The details of the malware were revealed in a blog post published by Google’s Threat Analysis Group (TAG), which specializes in tracking and exposing state-sponsored hacking.
TAG noted that the Cyber Azov app was created by Turla, a Kremlin-backed hacking group known for compromising European and American organizations with malware.
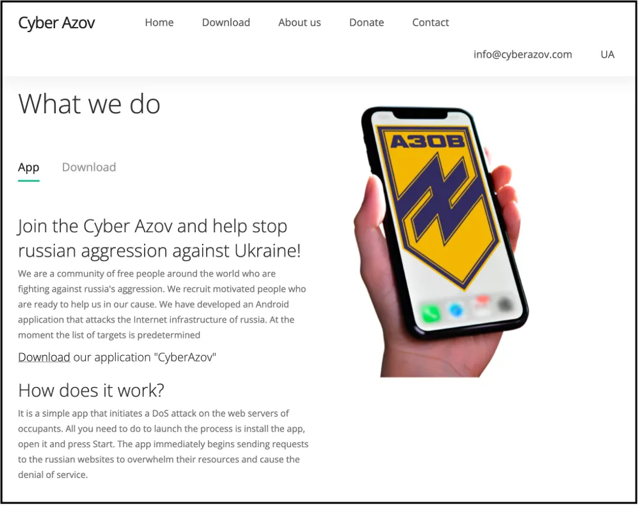
Text on the Cyber Azov website claimed the app would launch denial-of-service attacks on Russian websites, but TAG’s analysis showed that the app was ineffective for this purpose. A VirusTotal analysis of the APK file indicates that many of the biggest anti-malware providers flag it as a malicious app containing a Trojan.
TAG’s blog post suggests that the number of users who installed the app is small. However, the Cyber Azov domain was still accessible to The Verge on Tuesday morning, meaning more Android users could be tricked into downloading an app. A Bitcoin address listed on the website to solicit donations had not made or received any transactions at the time of publication.
The spoofed app tapped into a significant trend in the cyber dimension of the Russia-Ukraine conflict, namely the participation of a large decentralized base of digital volunteers hoping to aid the Ukrainian cause.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

