Samsung Security Hole Exposes 600 Million Devices to Hackers: Researcher [u]
Over 600 million Samsung smartphone owners have been exposed to hackers due to an unpatched security hole discovered by cybersecurity firm NowSecure. Actually, the flaw isn’t new: the researchers found it last fall and immediately notified Samsung about it (via the Wall Street Journal).
The risk, only now exposed for the first time, comes from a pre-installed keyboard, Swift, that cannot be disabled or uninstalled. On top of this, even if it is not used as the default keyboard it can still be exploited, the firm writes in the technical report.
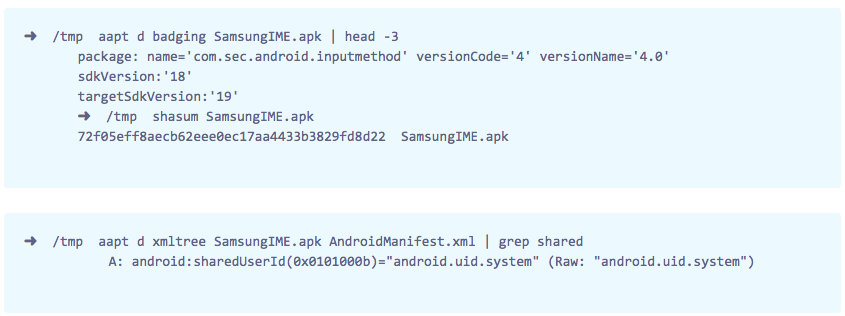
NowSecure’s Ryan Welton presented his findings at a Black Hat mobile security conference in London. The cybersecurity expert demonstrated that the unpatched security hole allows an attacker to remotely execute code as a system user, simply because Samsung didn’t encrypt the update process.
If the flaw in the keyboard is exploited, an attacker could remotely:
– Access sensors and resources like GPS, camera and microphone
– Secretly install malicious app(s) without the user knowing
– Tamper with how other apps work or how the phone works
– Eavesdrop on incoming/outgoing messages or voice calls
– Attempt to access sensitive personal data like pictures and text messages.
As detailed by NowSecure, the flaw affects Samsung S4, Mini, Galaxy S5 and even the recently released Galaxy S6: devices active on the network of the four incumbent carriers in the US. After purchasing two S6 smartphones from two different carriers, the researchers found that Samsung left the security hole in the software – this, despite their March 2015 claim of it being fixed.
It seems somewhat curious that, after informing Samsung on the matter in November 2014, the cybersecurity firm followed up with the manufacturer in December. Samsung, according to NowSecure CEO Andrew Hoog, asked for a year to fix it.
Update: SwiftKey told Forbes:
We’ve seen reports of a security issue related to the Samsung keyboard. We can confirm that the SwiftKey Keyboard apps available via Google Play or the Apple App Store are not affected by this vulnerability. We take reports of this manner very seriously and are currently investigating further.