
Apple’s iMessage Encryption Frustrates Drug Enforcement Administration
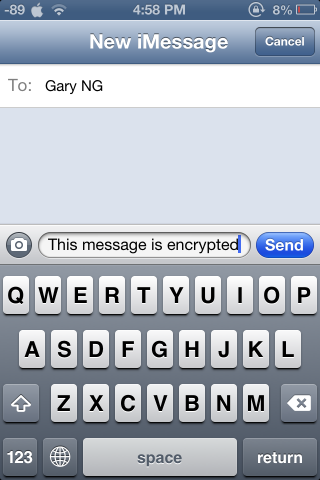
Officials with the DEA (Drug Enforcement Administration) reportedly complain that iMessages sent with Apple’s encrypted chat service are impossible to crack.
An internal document obtained by CNET, reads “it is impossible to intercept iMessages between two Apple devices,” even with a court warrant. The note is entitled, “Apple’s iMessages: A Challenge for DEA Intercept.”
Apple’s iMessage service came to the attention of the agency when its agents were drafting a court order to perform real-time electronic surveillance empowered by Title II of the Federal Wiretap Act, and discovered that they got incomplete records of text messages obtained from Verizon Wireless because the target of the investigation used iMessage.
Turns out text messages are impossible to intercept only when sent between two Apple devices. When the iMessage was sent to a non-Apple handset agents were sometimes able to intercept the message, “depending on where the intercept” was placed.
A year after iMessage was introduced in August last year, Mathew Green, a cryptographer, has pointed out that Apple didn’t provide information about how iMessage works.
“To me, the disconcerting thing about iMessage is how rapidly it’s gone from no deployment to securing billions of text messages for millions of users. And this despite the fact that the full protocol has never been published by Apple or (to my knowledge) vetted by security experts.”
iMessage was introduced with iOS 5, and encouraged users to avoid normal carrier SMS text messages and to route text through Apple instead. In January the company revealed how popular its messaging service had become: 2 billion iMessages sent each day from half a billion iOS devices, and Mac computers.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


I know this presents a challenge for law enforcement but, otherwise, I’m really happy to know that my messages between iOS devices are secure and private…. as they should be.
Indeed!
Definitely reassuring.
If there’s indeed a warrant, would it not be possible for the ISP to split the messages to both the intended recipient and the enforcement agency? If I recall the case law correctly, this is what was done to intercept RIM’s BBM messages.
It uses data, which means if someone were to be on a wifi network during sending the messages, they’re not routed through the carrier at all.
encryption is good. always.
now, cnet being able to obtain an “internal document”, these law enforcement agencies need to do good at securing their own confidential documents. needs some “encryption” somewhere 🙂