Chinese iOS Trojan Targets Jailbroken iPhones Used by Hong Kong Protesters
Lacoon Mobile Security has discovered a new ‘advanced’ Chinese iOS trojan targeting jailbroken iPhone users in Hong Kong, linked to a previous Android spyware app currently being distributed among protesters via a link shared on WhatsApp.
The simultaneous cross platform attacks on iOS and Android users is being carried out by Chinese-speaking attackers, suggesting a possible link to Chinese government cyber espionage, alludes Lacoon Mobile Security.
The Xsser mRAT is itself significant because it’s the first and most advanced, fully operational Chinese iOS trojan found to date. Although it shows initial signs of being a targeted attack on Chinese protesters, the full extent of how Xsser mRAT is being used is anyone’s guess. It can cross borders easily, and is possibly being operated by a Chinese-speaking entity to spy on individuals, foreign companies, or even entire governments.
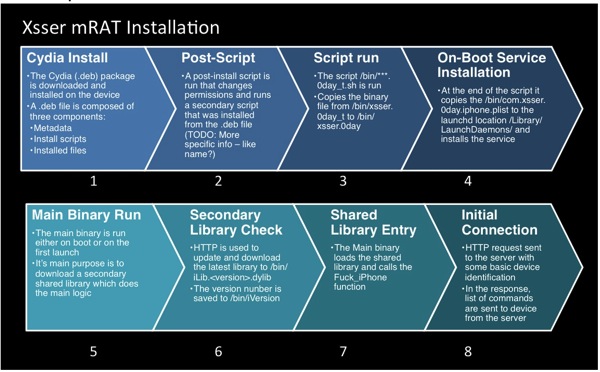
Lacoon says only jailbroken devices are susceptible to this trojan, but currently is unaware of how the trojan is being carried out. The user would need to add the trojan’s repository and install a package. Both iOS and Android attacks share a CnC server.
Lacoon hasn’t uncovered information regarding the method or vector of attack. The iOS device needs to be jailbroken in order to be infected. Then with Cydia installed, the repository would be need to be added and then the package could be installed. All that’s known is that both the iOS and Android attacks share a CnC server.
The package itself is a debian .deb package. The package installs an iOS ‘launchd’ service to make sure the app starts after booting and in addition starts it up immediately.
Information at risk for jailbroken users infected by this trojan, which runs after boot and is updated dynamically?
- Address book
- SMS messages
- Call logs
- Location Data (based on cell id)
- Pictures
- OS data
- Tencent Archive (a popular Chinese messaging app)
- Also passwords and other authentication info in the iOS keychains used by device accounts (AppleID, mail accounts and more) as well as the Phones GSM identities
Lacoon Chief Executive Michael Shaulov told Reuters “It is the first time in history that you actually see an operationalized iOS Trojan that is attributed to some kind of Chinese entity,” while he also noted infection is now targeting iOS devices instead of PCs.
The security firm says the the attacks could be deployed at other locations, but as of now, the Chinese link points to spying on current pro-democracy protesters in Hong Kong. Again, only jailbroken iOS users are being targeted, as non-jailbroken users remain safe from the trojan for now.
How to protect your jailbroken device? Remove the jailbreak by restoring your iPhone in iTunes.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!