
New Phishing Attack Uses Browser Autofill to Steal Data
Developer and hacker Viljami Kuosmanen from Finland, has found out that leading web browsers including Safari, Chrome and Opera, can all be tricked into giving away a user’s personal information through their profile-based autofill systems, The Guardian reports. He also discovered that some plugins and utilities such as LastPass, can also be tricked into giving out private information using the same phishing technique.
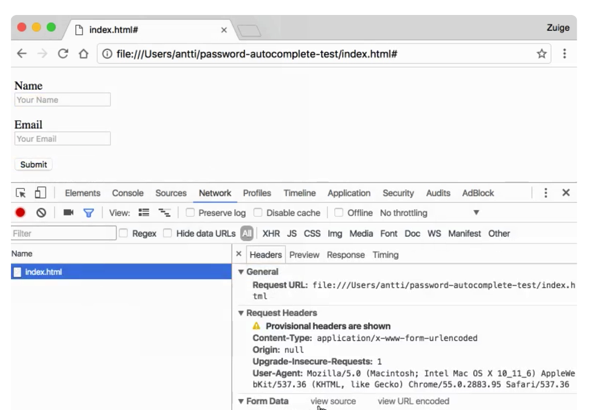
Kuosmanen explains that the phishing attack is quite simple. When a user tries to fill in information in some simple text boxes, such as name and email address, the autofill system will input other profile-based information into any other text boxes, even when those boxes are not visible on the page. As a result, the autofill system would be giving away much more sensitive information at the same time should the user confirm the autofill.
Be default, Chrome’s autofill system stores data on email addresses, phone numbers, mailing addresses, organisations as well as credit card information.
Mozilla’s Firefox is immune to the problem, as it does not yet have a multi-box autofill system and cannot be tricked into filling text boxes by programatic means, according to Mozilla principle security engineer Daniel Veditz. A more complete autofill system is currently in development for Firefox, however.
The phishing attack still relies on users being tricked into entering at least some information into an online form, but unsuspecting users could be tricked into entering more than they bargained for relatively easily. Users can protect themselves from this kind of phishing attack by disabling the autofill system within their browser or extension settings.
Kuosmanen has also set up a site to demonstrate the issue, showing a text box for a user’s name and email address, with text boxes for address and phonenumber hidden from view, autofilled by Chrome. You can check it out here.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

