
Security Researchers Find ‘Unpatchable’ Vulnerability in Nintendo Switch Consoles
Heads up, Nintendo Switch fans — you soon might be able to run custom ROMs on your Switch, or back up games to your own hard drives.
According to a new report from Ars Technica, hackers have revealed how the Nintendo Switch can be made to run arbitrary code through an exploit of an unpatchable flaw in the console’s Nvidia Tegra X1 chip.
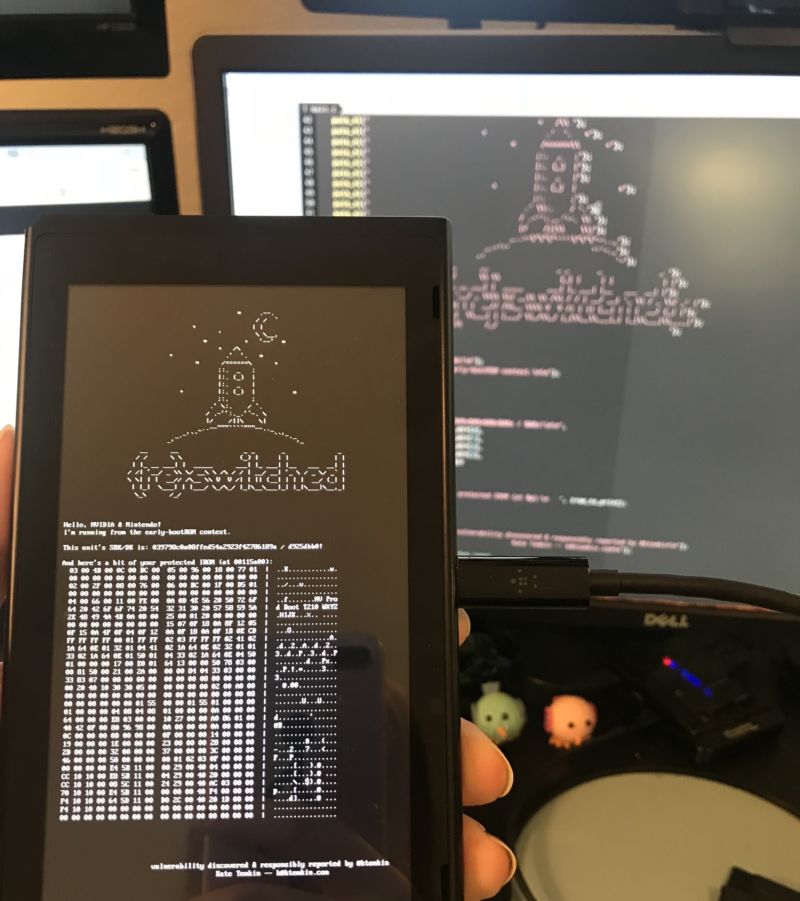
Hardware hacker Katherine Temkin and the hacking team at ReSwitched have released an extensive outline of what they’re calling the “Fusée Gelée” coldboot vulnerability earlier today, alongside a proof-of-concept payload that can be used on the Switch.
Here’s the summary from github:
This report documents Fusée Gelée, a coldboot vulnerability that allows full, unauthenticated arbitrary code execution from an early bootROM context via Tegra Recovery Mode (RCM) on NVIDIA’s Tegra line of embedded processors. As this vulnerability allows arbitrary code execution on the Boot and Power Management Processor (BPMP) before any lock-outs take effect, this vulnerability compromises the entire root-of-trust for each processor, and allows exfiltration of secrets e.g. burned into device fuses.
“Fusée Gelée isn’t a perfect, ‘holy grail’ exploit—though in some cases it can be pretty damned close,” Temkin writes in an accompanying FAQ.
One reason why this is such a troublesome hack for both Nintendo and Nvidia is how it’s seemingly unfixable. Because the hack makes use of an exploit in the Tegra X1 bootROM, it can’t be modified once it leaves manufacturing. This means there are 14.8 million Switches out there that are vulnerable to the exploit and could be hacked to run a whole manner of different games and programs.
Temkin is also working on a custom ROM for the Switch that she’s calling “Atmosphère.” Once it and the full version of Fusée Gelée are publicly revealed, it’ll be open season on Mario.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


Time to buy a Switch
Great news. I still keep my iPhone 5 around since it’s jailbroken – so much more useful. Love having the weather in the status bar (since there’s no notch, there’s plenty of room for it) Replacing Siri with Google Assistant on the Home Button is amazing and having a new wallpaper loaded from Bing everyday is fun. Replacing “FIDO” with the name of the WiFi network I’m connected to is also an obvious improvement. I know I have Fido – I pay them every month, how can I forget? Jailbroken Switch should be similarly great.
You could get pretty much all that with an Android, running latest software, on an amazing hardware, without notch… If you want to go even further, you could also root it and get even more out of it
Yup. I was gonna say, looks like he really just wants an Android.
Jailbroken iPhone > rooted Android.
It’s really a matter of opinion. I didn’t know people still did iPhone vs Android debates in the comments lol
I’m still trying to figure out why he brought up this in a switch article
Some would argue it’s an iPhone website so that’s why… But…still doesn’t match the article in question haha
It’s the article that doesn’t fit. I was fixing that 😉
Stock Android > Jailbroken or Stock iPhone.
As much as I agree, it’s again a matter of opinion.
Absolutely correct. I’ve suggested iPhones to many people, despite my dislike for them. Some people just require simple without the ability to get lost in features.
But if you’re going through all the trouble of jailbreak just to get Android features… Might as well just get an Android
People have already been doing this to their switch to run old games and use the internet….