
Chinese Hackers Exploit Microsoft Key, Target US Government Officials
Microsoft finds itself embroiled in a major cybersecurity incident as China-backed hackers successfully exploited a key, granting them unauthorized access to email inboxes of various US government agencies.
According to reports, U.S. Commerce Secretary Gina Raimondo, U.S. State Department officials, and undisclosed organizations were among the targets (via TechCrunch).
Microsoft disclosed the breach last week, linking it to an espionage group named Storm-0558, which the company believes has strong ties to China. The exact method used by the hackers to obtain the Microsoft signing key remains under investigation.
The hacking activities, which began in mid-May, were acknowledged by the U.S. Cybersecurity and Infrastructure Security Agency (CISA), confirming that a small number of government accounts were compromised, resulting in the exfiltration of unclassified email data.
While China’s foreign ministry denied the allegations, previous instances have shown China’s utilization of unknown vulnerabilities to hack into Microsoft-powered email servers.

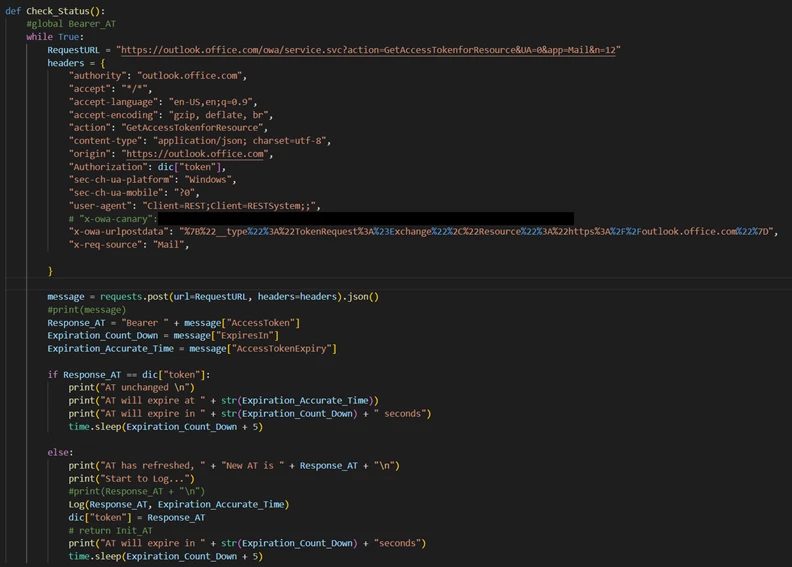
Microsoft’s investigation revealed that the hackers acquired one of its consumer signing keys, known as an MSA key, initially used to secure consumer email accounts like Outlook.com.
Surprisingly, the hackers exploited this consumer key to forge tokens that granted them access to enterprise inboxes, despite Microsoft’s initial belief that an enterprise signing key had been compromised.
Microsoft claims to have successfully blocked all unauthorized activity related to the incident, indicating that the hackers have lost access.
As the situation stabilizes, Microsoft now faces scrutiny over its handling of the breach, which is considered one of the largest breaches of unclassified government data since the SolarWinds attack in 2020.
The company has received criticism for its careful choice of words in its blog post, avoiding terms like “zero-day” and downplaying the severity of the vulnerability.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

