
Here’s How the Evasi0n iOS 6.1 Jailbreak Was Achieved
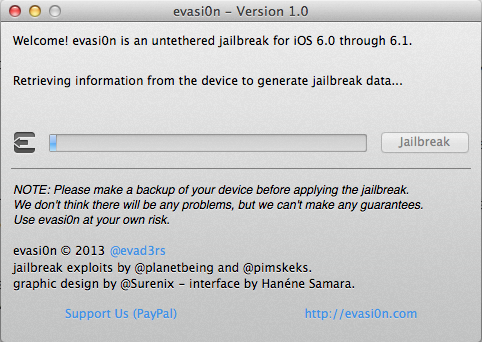
Earlier today the @evad3rs team released their untethered iOS 6.1 jailbreak tool, evasi0n 1.0–one of the easiest to date. Just how was this latest jailbreak accomplished? Braden Thomas, from Accuvant Labs, explains what @planetbeing, @pod2g @pimskeks and @musclenerd were able to figure out to bypass Apple and iOS to reach an untethered jailbreak:
This blog post will focus on the evasi0n userland component. Evasi0n’s userland component is very unique, because it is entirely filesystem-based. It doesn’t require memory corruption to escalate privileges from mobile to root. Perhaps it was named evasi0n because it evades all the userland exploit defenses instead of attacking them head-on.
Evasi0n works in 3 stages that are described below. All of the stages use functionality on the phone exposed by MobileBackup, the daemon used to backup user data from the device, and restore backups back to the device. Since backups are created by the user’s device, and must be interchangeable between devices, they cannot be easily cryptographically signed, so they are essentially untrusted data.
Definitely an interesting and complex read, for those that can understand all of it. These guys are brilliant.
[via Daring Fireball]
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


Has no one noticed when the jailbreak the time is wrong, I’m having the same issue, anyone know why??? Thanks
Not sure why it occured, but I fixed by toggling “set automatically” off and on.