
Apple: Fix for OS X Mavericks SSL Security Flaw Coming “Very Soon”
After releasing iOS 7.0.6 to fix an SSL security issue, OS X Mavericks still has not been updated to close the security flaw.
Apple has started to tell news outlets such as Reuters and Re/code an OS X software update is on the way:
“We are aware of this issue and already have a software fix that will be released very soon,” Apple spokeswoman Trudy Muller said.
Despite some speculating this SSL bug could have been a National Security Agency ‘backdoor’, Muller declined to respond those theories according to Reuters.
John Gruber brings up ‘five levels of paranoia’ related to this SSL incident on iOS, as the timing of the vulnerability coincides with earlier claims the NSA had an Apple backdoor in the PRISM report leaked by Edward Snowden.
I see five levels of paranoia:
1. Nothing. The NSA was not aware of this vulnerability.
2. The NSA knew about it, but never exploited it.
3. The NSA knew about it, and exploited it.
4. NSA itself planted it surreptitiously.
4. Apple, complicit with the NSA, added it.Me, I’ll go as far as #3. In fact, I think that’s actually the optimistic scenario — because we know from the PRISM slides that the NSA claims some ability to do what this vulnerability would allow. So if this bug, now closed, is not what the NSA was exploiting, it means there might exist some other vulnerability that remains open.
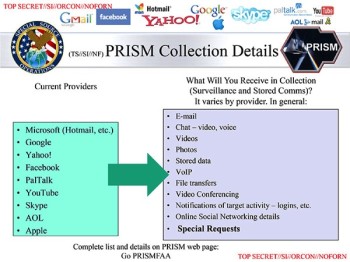
iOS 6 was released in September 2012, while a month later the NSA ‘added’ Apple to its PRISM program PowerPoint slide. Conspiracy theorists, start brewing the coffee.
If you haven’t updated your iOS device to 7.0.6, you should do so right away. Also, only connected to trusted Wi-Fi networks to further protect yourself.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

