
Apple AirTag Security Flaw Allows Phishing Attack: Researcher
As discovered and highlighted by security researcher Bobby Rauch, a bug in Apple AirTag’s ‘Lost Mode’ could allow a hacker to lead unsuspecting users to an iCloud phishing page.
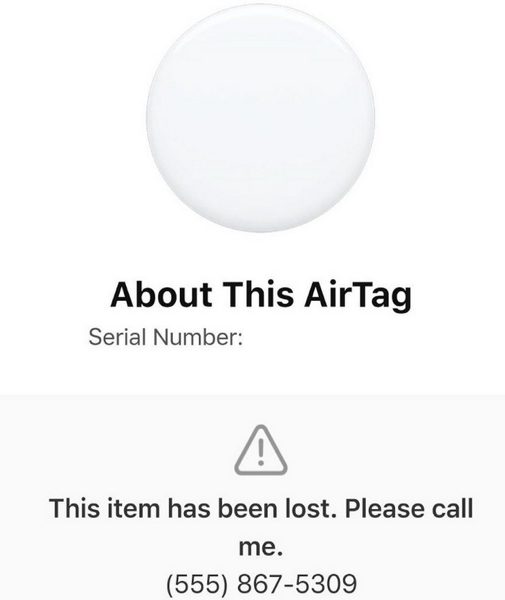
According to Apple, the AirTag’s Lost Mode allows someone who finds a misplaced AirTag to take steps to locate it and return it to the user. Enabling Lost Mode displays a phone number or address on a specialized found.apple.com website.
According to Rauch, however, the AirTag’s Lost Mode “doesn’t currently stop users from injecting arbitrary computer code into its phone number field,” which could lead an unsuspecting AirTag retriever to a phishing site.
“In the modern telling of this caper, a weaponized AirTag tracking device could be used to redirect the Good Samaritan to a phishing page, or to a website that tries to foist malicious software onto her device.”
In other words, a hacker could add a code that sends users to a phishing site that mimics Apple’s iCloud login site to steal their username and password.
Apple has not yet issued any official comment regarding the issue.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

