
Here’s How Stolen iPhones are Being Wiped Clean for Resale
Security researchers at Trend Micro have uncovered an interesting set of tools and services being used by criminals to break open iCloud accounts and unlock stolen iPhones before reselling them. According to ZDNet, the researchers have found that at the core, the attack chain “harnesses a victim’s panic to take over these devices”, starting with a spoofed Apple email or text, notifying the victim that their device has been found.
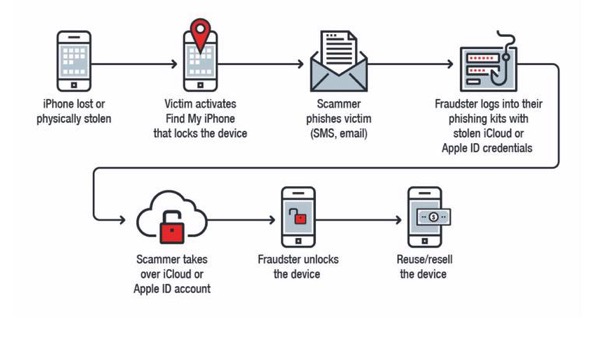
In most cases, victims desperate to get their lost iPhone back click on a link which requires their iCloud account credentials. The criminals then use these stolen details to access and compromise the iCloud account, as well as to unlock and eventually wipe clean the stolen iPhone.
Researchers say that these iCloud phishers run their business using a set of cybercriminal tools that include MagicApp, Applekit, and Find My iPhone (FMI.php) framework to automate iCloud unlocks in order to resell the device in underground and gray markets.
The team explored three such services online and found that while they had a global customer base of thieves, they also rented out servers to send phishing messages. The groups behind these services appear to be based in Kosovo, the Philippines, India, and North Africa. Once a tool has been purchased, the target iCloud account can be hijacked, content downloaded for other malicious activities, and also deleted outright.
“Just as the internet has evolved the way information is accessed and how businesses are conducted, it has also blurred the face of crime,” Trend Micro says.
While no vulnerabilities or bugs are being exploited to conduct these criminal campaigns, Apple has already been made aware of the research.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


Jesus
well, don’t lose your phone
Or don’t click on a phishing link (check the URL)
how many times have people been told not to click a login link from an email?