
Apple Turns on App Store Encryption to Address Security Flaw
Apple has fixed a flaw in its App Store application by turning on encryption to protect its users from privacy and security attacks over public Wi-Fi networks (via CNET).
The flaw was reported last July by Elie Bursztein, who works at Google as a security researcher. The timing of his blog post reporting the Apple fix is interesting, though: it comes just a day after Apple’s head of worldwide marketing, Phil Schiller, tweeted “be safe out there,” and pointed to the F-Secure report that highlights the rise in malware for Android. In this context, Bursztein’s post can be taken as a public response to Schiller’s tweet.
Apple fixed the security flaw in a January update, saying that “active content is now served over HTTPS by default” and thanked Bursztein, Bernhard Brehm of Recurity Labs, and Rahul Iyer of Bejoi LLC for reporting this issue.
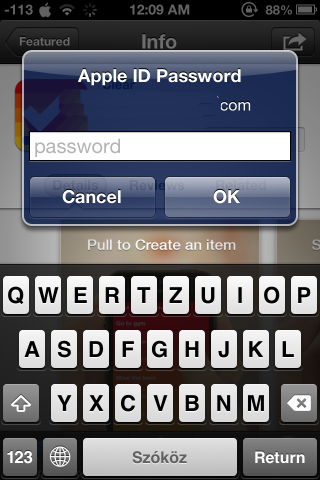
The security flaw arose because Apple opted not to use encryption when the iOS user connects to the App Store using their iOS device. Bursztein’s blog post highlights that the flaw made iOS users vulnerable to privacy and security attacks, and he even made the effort to demonstrate each one of them.
Bursztein’s blog post highlights the risk of public networks, including airport and coffee-shop networks, as hackers only have to be on the same network with their victims to launch an attack.
And the lack of encryption Bursztein highlights has made iOS users vulnerable to App Store password theft, app swapping, fake app upgrades, prevention of application installation, and privacy leaks.

By publicizing this flaw, Bursztein highlighted the necessity for encrypted connections and their importance for mobile apps as well.

