
Zero-Day iOS Exploit Reportedly Sells for $500,000
In the market of information about computer vulnerabilities, the days of handing over knowledge of a zero-day bug for a T-Shirt or perhaps honorable mention on the company’s website are over. Finding zero-day bugs has become a business, and some — like two Italian hackers — have really benefited from it. When it comes to iOS exploits, some hackers just cashed in $500,000 for a zero-day iOS bug they discovered, The New York Times reports (via Reddit).
The hackers, Luigi Auriemma, 32, and Donato Ferrante, 28, sell technical details of such vulnerabilities to countries that want to break into the computer systems of foreign adversaries. The two will not reveal the clients of their company, ReVuln, but big buyers of services like theirs include the National Security Agency — which seeks the flaws for America’s growing arsenal of cyberweapons — and American adversaries like the Revolutionary Guards of Iran.
All over the world, from South Africa to South Korea, business is booming in what hackers call “zero days,” the coding flaws in software like Microsoft Windows that can give a buyer unfettered access to a computer and any business, agency or individual dependent on one.
The article points to a rocketing business in zero-day exploits. A hacker needs to weigh his options: he can contact tech companies which have Zero-day initiatives such as Microsoft, or he can hand over the information through some ‘pseudonymous’ exploit broker who will hand the information over to a government agency, keep his mouth shut, forget to ask too many questions and get paid a half million dollars.
As Andy Greenberg of Forbes pointed out last year, there is a price set by tech companies for zero-day bugs, but iOS exploits are the most coveted. Last year an iOS exploit brought a quarter of a million for the hacker who found the bug. This year the price went up to $500,000 according to the NYT’s sources.
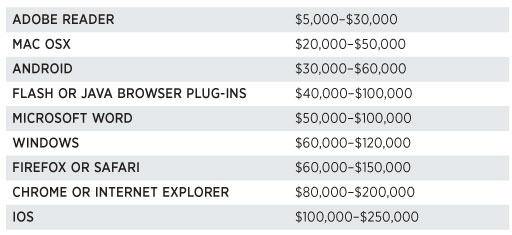
Price list for zero-day exploits (2012) via Forbes
From this perspective I can only respect the Evad3rds. They did it for free, for all of us who were willing to unleash the potential of iOS, and they did it for a simple entry on Apple’s website. You may recall that Apple credited the Evad3rs for pointing to iOS 6 flaws when issuing the iOS 6.1.3 software update.
Since Apple does not have a program to pay hackers for discovering vulnerabilities in iOS, I can only respect Pod2g and fellow Canadian planetbeing for doing that tremendous amount of work under pressure from the jailbreak community.

