
How to Check if your Version of Xcode is Legitimate
Following the first attack on the App Store, Apple has reacted by informing developers that it has removed apps built with the counterfeit version of Xcode and says that it plans to take further steps to prevent attacks.
You may recall that earlier last week a security firm published a list of malware-infected apps built with a counterfeit version of Xcode called XcodeGhost. The security firm suggested there are hundreds of infected apps in the Chinese App Store, but so far only 25 have been identified. Apple has removed all of them, and customers can delete and update them, Phil Schiller, Apple’s head of worldwide marketing said in an interview with Sina and cited by Reuters.
He said that Apple will offer domestic downloads of its developer toolkit from China, according to an interview with Chinese news site Sina.com.
Schiller also said that the company knows of no cases where tainted apps have been used to transmit customer data.
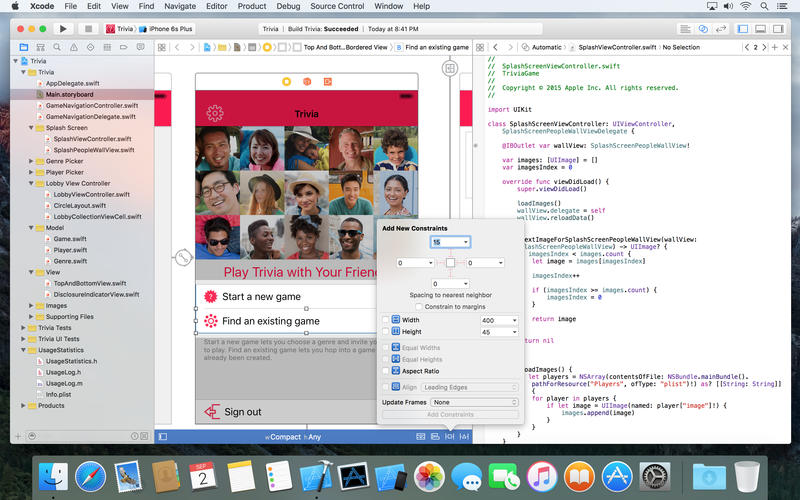
Also, Apple posted a message to developers asking them to always download Xcode directly from the Mac App Store or from the Apple Developer website and to leave Gatekeeper enabled on all systems, as OS X automatically validates the code signature for the developer tool.
To check the validity of your current copy of Xcode, Apple recommends you type the following command in Terminal, but once again, you need to have Gatekeeper enabled: spctl –assess –verbose /Applications/Xcode.app (“Applications” is the directory where Xcode is installed).
If legit, you should get a message like this /Applications/Xcode.app: accepted source=Mac App Store (note that “accepted” is the keyword in this case).
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


Or answer the question: “Did the developer download the Xcode compiler from a Chinese bulletin board in the .cn domain?”
Or: “Did you download Xcode from Geocities? If yes, then your Xcode is counterfeit.”