Bash Security Flaw Leaves OS X and Linux and More Open to Attack
If you thought that Heartbleed was the biggest bug yet discovered, you may want to think again: Red Hat security researchers have revealed a new bug called “bash bug”, which they say easily matches Heartbleed.
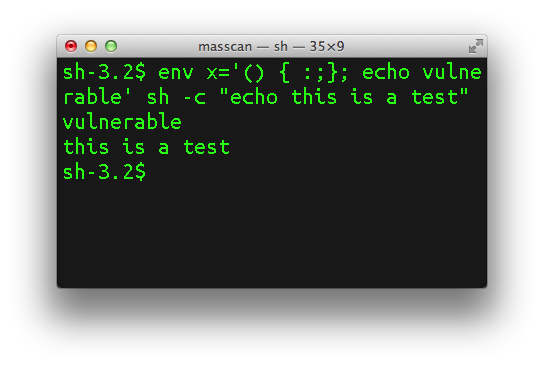
The common Unix command shell “bash” used by Linux and Mac users allows attackers run any code they want as soon as the shell starts running and, therefore, obtain control of any connected devices that run bash.
Robert Graham has discussed the issue on his blog noting that the “bash bug” is as big as Heartbleed, if not bigger, and that it has been around for a long, long time.
Internet-of-things devices like video cameras are especially vulnerable because a lot of their software is built from web-enabled bash scripts. Thus, not only are they less likely to be patched, they are more likely to expose the vulnerability to the outside world.
Unlike Heartbleed, which only affected a specific version of OpenSSL, this bash bug has been around for a long, long time. That means there are lots of old devices on the network vulnerable to this bug. The number of systems needing to be patched, but which won’t be, is much larger than Heartbleed.
There are already patches for some Linux variants, and big Internet services such as Akamai have already taken action. But this doesn’t mean that some older servers and other internet-connected devices will be protected. At this moment is hard to estimate the potential damage.