This Bug Lets Anyone Bypass iPhone, iPad Activation Lock
A newly discovered iOS bug can be used to bypass the Activation Lock feature on iPhones and iPads, giving access to the homescreen of locked devices running the latest version of iOS. As detailed by SecurityWeek, there are at least two variations of the vulnerability, one of which works on iOS 10.1, while the second one has been successfully reproduced on the latest 10.1.1.
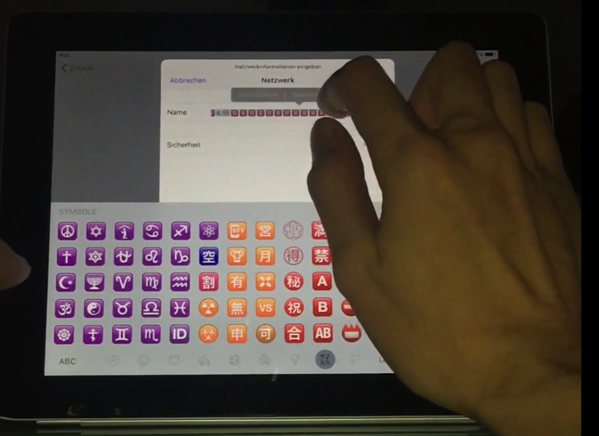
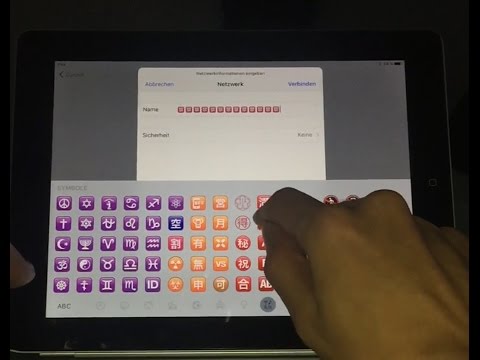
The Activation Lock feature in iOS devices is enabled automatically when Lost Mode is used, preventing reactivation of the device without the owner’s permission. When a locked device is started, users are prompted to connect to a Wi-Fi network. If the “Other Network” option is selected, users are required to enter the name of the network and choose a security protocol, followed by a username and password prompt.
The problem, as researchers discovered, is that there is no limitation on the number of characters that can be entered into the name, username and password fields. By entering very long strings into these fields, an attacker can trigger a crash that exposes the device’s homescreen. The crash can be triggered using at least two methods. The first involves Apple’s iPad smart cases, which cause the device to wake or sleep when the case is opened or closed.
This method worked on iOS 10.1, but the bug was addressed in iOS 10.1.1, which Apple released on October 31. Researchers at Vulnerability Lab also analyzed the issue and discovered that it can be reproduced on iOS 10.1.1 using the screen rotation feature and Night Shift mode.
The following video shows how the bug is triggered on an iPad, although it works on iPhones as well: