
Google Docs on the Web Getting More Markdown Support

Google on Tuesday announced Markdown support for Google Docs on the web, allowing users to format text using plain-text shortcuts instead of keyboard shortcuts or UI buttons (via The Verge).
Markdown is a pretty straightforward plain-text markup language that was created in 2004 by John Gruber and Aaron Swartz to format text with simple character shortcuts.
Google Docs for the web already supported some Markdown shortcuts for bulleted lists, numbered lists, and checkboxes. Expanded support will now let you use Markdown to add headings, bold text, italicize text, strikethrough, and add links to text. While that is far from everything Markdown is capable of, it covers everything most users would want to use the language for.
Google says it is adding Markdown support through the autocorrect feature in Docs, which will now automatically detect the language and format text accordingly as you type. Here’s a little Markdown guide for the uninitiated:
# Text preceded by a pound sign will be automatically converted into a level one heading
*Text between asterisks will be bold.*
_Text between underscores will be italicized_
–Text between hyphens will be strikethrough–
[This text will be hyperlinked](Link)
If you’ve used Markdown elsewhere (WhatsApp supports it too!), Google’s implementation should feel pretty familiar. Except for strikethrough, of course — for some reason, Google decided to use the hyphen (-) for strikethrough instead of the tilde (~) symbol like most Markdown implementations.
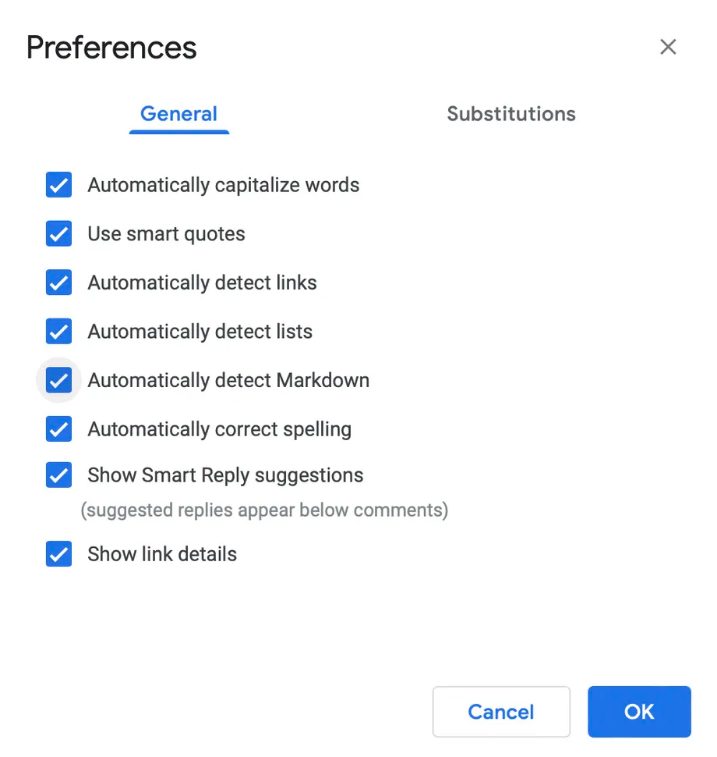
Google says it could take “longer than 15 days” for the feature to roll out to everyone. Even when you do get it, it will be disabled by default. To activate Markdown detection in Google Docs, open a document, go to Tools > Preferences, and check the Automatically detect Markdown box.
According to Google, expanded Markdown support is coming to “Google Workspace customers, as well as legacy G Suite Basic and Business customers,” in addition to personal accounts.
Google today also launched version 100 of Chrome, which changes the web browser’s logo for the first time since 2014. The tech giant also released an emergency update for Chrome last week to patch a high-severity zero-day vulnerability being exploited in the wild.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

