
Google Patches Zero-Day Security Exploit in Chrome for Mac and Windows
Google is rolling out Chrome version 103.0.5060.114 on Windows to patch a high-severity zero-day vulnerability being actively exploited in the wild — reports BleepingComputer.
A zero-day is a security hole that is unknown to the company–and thusly a major flaw as the exploit allows it to be open and out in the wild until patched.
The security flaw in question, being tracked as CVE-2022-2294, is a heap-based buffer overflow vulnerability in Chrome’s Web Real-Time Communications (WebRTC) component. It can be exploited to cause program crashes, execute arbitrary code, and even bypass security solutions by executing malicious code.
“Google is aware that an exploit for CVE-2022-2294 exists in the wild,” the company said in a security advisory published on Monday. The zero-day vulnerability was reported by the Avast Threat Intelligence team’s Jan Vojtesek on July 1.
Updating Chrome will patch the vulnerability on your Windows machine. Google Chrome version 103.0.5060.114 was available to download when iPhone in Canada checked for available updates at the time of writing.
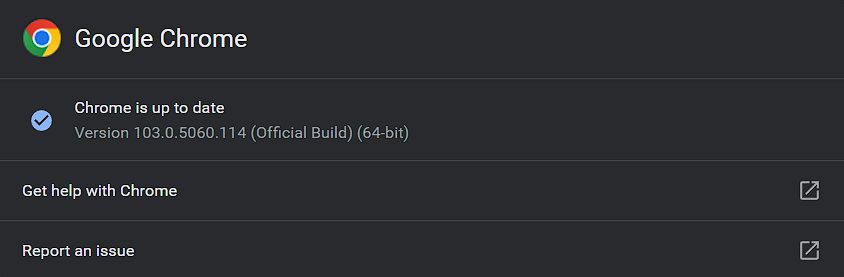
To manually check for and install the update, open the Chrome menu (three vertically-aligned dots in the toolbar) and go to Help > About Google Chrome. Chrome will check for updates, download any that are available, and prompt you for a restart to install them. The browser will also automatically check for and install available updates at launch.
Google will refrain from divulging details regarding this exploit until the update has made its way to the majority of Chrome’s Windows user base. “Access to bug details and links may be kept restricted until a majority of users are updated with a fix,” Google said.
“We will also retain restrictions if the bug exists in a third-party library that other projects similarly depend on, but haven’t yet fixed.”
This is the fourth Chrome zero-day Google has dealt with so far this year. The company released an emergency Chrome update in April to patch CVE-2022-1364, and another in March to fix CVE-2022-1096. Both of those vulnerabilities were also being actively exploited before Google plugged them.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

