
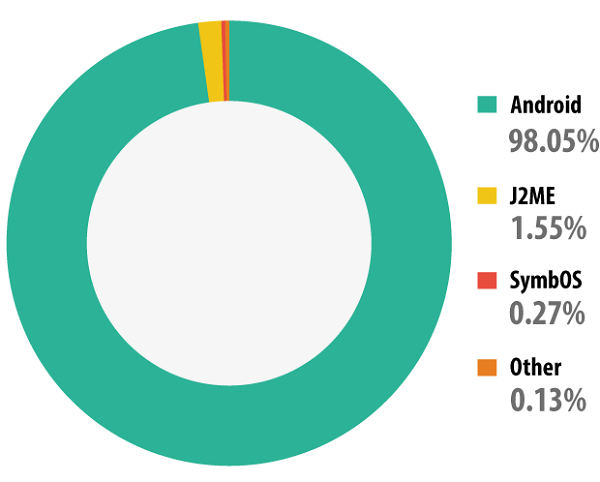
Kaspersky: Android is Targeted by 98% of Mobile Malware
According to a new mobile malware evolution report from Kaspersky Labs, 98% of mobile malware is targeted at Android devices, majority of which is designed to steal users’ money, including SMS-Trojans, and tons of backdoors and Trojans (via ComputerWorld). The report highlights that Android remained the prime target for malicious attacks in 2013, confirming the vulnerability of its architecture.
Kaspersky notes that different installation packages can install programs with the same functionality that differ “only in terms of the malicious app interface and the content of the text messages it spreads”. Over the year, the number of mobile malware modifications designed for phishing, the theft of credit card information and money increased by a factor of 19.7.
The report further points out that 2013 not only saw a significant increase in output from mobile virus writers, but also saw them applying methods and technologies that “allowed cybercriminals to use their malware more effectively”.
“Android vulnerabilities are used by criminals for three main reasons: to bypass the code integrity check when installing an application (vulnerability Master Key); to enhance the rights of malicious applications, considerably extending their capabilities; and to make it more difficult to remove malware. For example, Svpeng uses a previously unknown vulnerability to protect itself from being removed manually or by the antivirus program.
Cybercriminals also exploit the Master Key vulnerability and have learned to embed unsigned executable files in Android installation packages.”
It is also unfortunate for Android users that the only way to get rid of vulnerabilities in Google’s mobile platform is by receiving an update from the device manufacturers.

