
Powerful Spyware App Said to be Targeting iPhone Users
Researchers at mobile security firm Lookout have discovered that a powerful spyware app that was initially designed for Android devices is now also targeting iPhone users. The surveillance app’s developer is said to have abused the Apple-issued enterprise certificates to bypass the App Store and infect the victims (via TechCrunch).
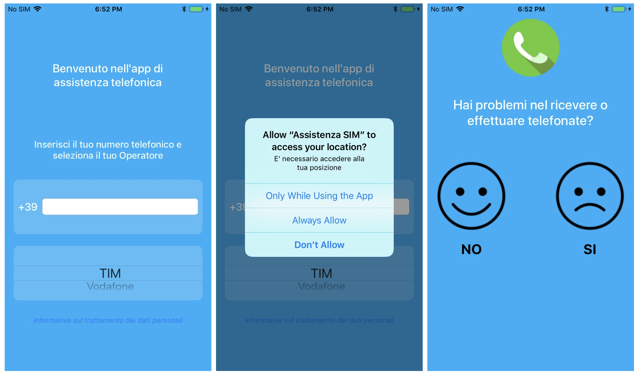
Security researchers say that the spy app quietly grabs the victim’s contacts, audio recordings, photos, videos, and other device information, including their real-time location data.
The malicious app, which can also be remotely triggered to listen in on people’s conversations, was apparently served from fake sites purporting to be cell carriers in Italy and Turkmenistan. Researchers are linking the app to Connexxa, the makers of a previously discovered Android app which is known to be used by the Italian authorities:
The Android app, dubbed Exodus, ensnared hundreds of victims — either by installing it or having it installed. Both of the apps use the same backend infrastructure, while the iOS app used several techniques — like certificate pinning — to make it difficult to analyze the network traffic, Adam Bauer, Lookout’s senior staff security intelligence engineer, told TechCrunch.
Researchers say that Connexxa signed the app with an enterprise certificate issued by Apple, allowing the surveillance app maker to bypass Apple’s strict app store checks.
Apple has now revoked the app maker’s enterprise certificate, knocking every installed app offline and unable to run.

