
iTunes Security Flaw Sees Unencrypted Password Transmissions: Researcher
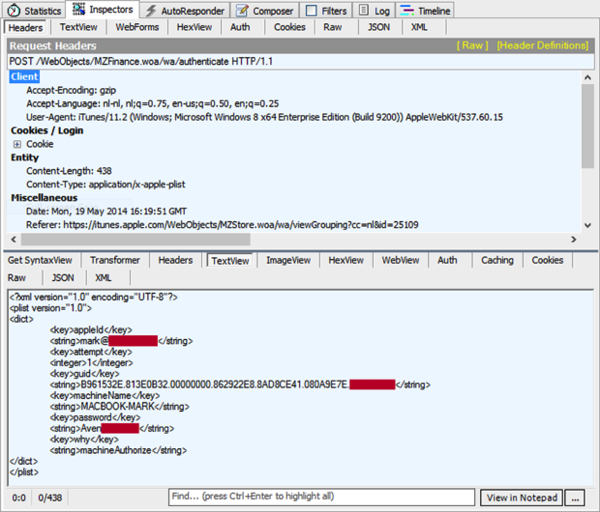
iTunes users on Windows are vulnerable to a serious SSL certificate flaw that allows hackers to intercept their passwords, which are easy to intercept because Apple doesn’t hash passwords before sending them to the server. This leaves the SSL connection vulnerable to a man-in-the-middle attack, according to security researcher Mark Loman as reported by Dutch site Tweakers.
You may recall that when Apple pushed out iOS 7.1.1, it also fixed a serious security flaw in its mobile operating system that left iDevice users vulnerable to man-in-the-middle attacks, allowing a hacker with privileged network position to capture data or change the operations performed in sessions protected by SSL.
With iOS 7.1.1, Apple has apparently patched this issue on mobile devices but left out the patch for the certificate vulnerability on iTunes.
After looking into some claims of the jailbreak community, Mark Loman decided to do some investigating of his own and made a shocking discovery. SSL has two tasks: one, to verify communication with the intended server; and two, to prevent manipulation.
“I was asked to look into a claim coming from hackers, that they ‘hacked’ iCloud, he tells iPhone in Canada. “These hackers did not want to talk about the vulnerability they are using but this vulnerability is actually a pretty big hole…”
What Mark discovered is that Apple forgot step one: the basis of secure communication. When we contacted him for clarification, Mark pointed to the core issue:
“The problem is with verifying the certificate. Apple appears to have deliberately left out this essential step required for proper secure communication. They fixed it last month for iOS but forgot to fix it for iTunes. But the jailbreak community is already making use of it — which is how I figured it out.”
Loman also questions whether this flaw was an accidental mistake or if it was possibly ‘done on purpose’:
“This is either a beginner’s mistake, or it was done on purpose,” he tells Tweakers. “Intelligence agencies like the NSA can thus easily intercept all communication via iCloud.”
Also, the passwords are sent unencrypted not only when buying music on iTunes, but also when activating a new iOS device using iTunes. According to Mark Loman of Dutch security company SurfRight, the flaw only concerns Windows users, as OS X users are warned that the certificate is incorrect.
Apparently, this certificate vulnerability is so serious that it allows hackers to unlock stolen iPhones that were previously locked by Apple or the previous owners as they were reported lost.
Apple is aware of the issue but remained silent when contacted by Mark and several newspapers.
Loman suspects that this is the exact same vulnerability Apple patched up in iOS recently. For those who have skipped the latest update, Loman’s message is: Don’t use public Wi-Fi, because you are vulnerable to a man-in-the-middle attack. And so there are older iOS devices such as the iPad 1 and the iPhone 3GS that cannot be updated to the latest iOS.
Loman noted he has a full report coming tomorrow, to be published in a Dutch newspaper. More to follow…
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

