
Dev Team Confirms 3.0 Jailbreak, Warns Against Fakes
Recently Apple released a second beta version of 3.0 firmware to developers. This new release is much improved and fixes a lot of bugs from the original beta. Just what is the deal with jailbreaking OS 3.0? Well yesterday the iPhone Dev Team confirmed that 3.0 beta can indeed be jailbroken–again.
The Dev Team goes on to explain that the exploits they use to jailbreak the iPhone are at the hardware level, not software. So that means until Apple debuts the iPhone 4G, jailbreaking of the iPhone 3G will continue. However, there is one extremely important piece of information everybody needs to know about the 3.0 jailbreak.
The Dev Team was quick to point out the following:
THE MOST IMPORTANT THING ABOUT THE UNOFFICIAL QUICKPWN RELEASES IS THAT IF YOU USE THEM, YOU WILL KILL YELLOWSN0W, POSSIBLY FOREVER. That’s because QuickPwn, by its very nature, requires you to already have accepted Apple’s official IPSW, along with its baseband update. If you do that, you will (possibly forever) lose your ability to software-unlock your iPhone 3G.
Yep, you got that right. Some sites out there, such as quickpwn dot com are NOT the “official” developers of QuickPwn. The only blog you should trust for information is the Dev Team blog. Using these unnofficial releases can lock your iPhone forever, meaning you won’t be able to use it with ANY carrier.
Why Isn’t There An Updated Version of QuickPwn for OS 3.0?
The Dev Team says they avoided releasing an updated version of QuickPwn/PwnageTool for OS 3.0 beta because–it’s still in beta! There’s no point in releasing multiple versions everytime the betas are updated. If you want QuickPWN, the Dev Team will release it when the final version of 3.0 comes this summer. Done. Like. Dinner.
So there you have it folks, if you’re looking to download QuickPwn, only do it from this URL: http://blog.iphone-dev.org, and nothing else. Now you can tell your friends “didn’t you get the memo?” when they start pushing unofficial QuickPwn websites on you!
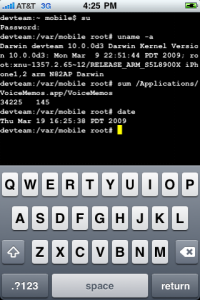
Don’t worry, I don’t know what’s going on with the screenshot above, either. 😉
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


Head on over to the forums if any questions or discussions 😉
Good job Dev Team, keep up the good work!
Head on over to the forums if any questions or discussions 😉
Good job Dev Team, keep up the good work!