
Google Releases Another Emergency Chrome Update to Fix Zero-Day Vulnerability
Google is rolling out version 100.0.4896.127 of its Chrome browser for Windows, Mac, and Linux as an emergency update to patch a high-severity zero-day vulnerability — reports The Register.
The update fixes a type confusion vulnerability, tracked as CVE-2022-1364, in Chromium V8 that impacts the JavaScript engine used in Chrome and other Chromium-based browsers like Microsoft Edge, Brave and Vivaldi. CVE-2022-1364 was identified as a high-severity, zero-day bug that is actively being abused by attackers in the wild.
Type confusion vulnerabilities like CVE-2022-1364 can cause a browser to crash or trigger local errors, and can potentially be exploited by bad actors to execute arbitrary code.
“Depending on the privileges associated with the application, an attacker could view, change, or delete data,” according to the Center for Internet Security. “If this application has been configured to have fewer user rights on the system, exploitation of the most severe of this vulnerability could have less impact than if it was configured with administrative rights.”
Clement Lecigne, a member of Google’s Threat Analysis Group (TAG), reported the vulnerability on April 13 and the company announced the fix on the same day. “Google is aware that an exploit for CVE-2022-1364 exists in the wild,” the tech giant wrote in an alert.
The update had already been installed when iPhone in Canada checked for available updates in Chrome.
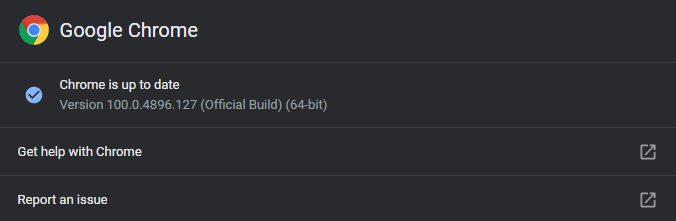
To manually check for and install the update, open the Chrome menu (three vertically-aligned dots in the toolbar) and go to Help > About Google Chrome. Chrome will check for updates and automatically install any that are available. The browser will also automatically check for and install available updates at launch.
Google said it won’t share further details regarding the flaw until the majority of users are inoculated against the vulnerability. The company added that it “will retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed.”
This is the third Chrome zero-day Google has patched so far this year. Google last month issued an emergency update to fix CVE-2022-1096, which was also being actively exploited.
The company also had to patch a particularly garish zero-day, tracked as CVE-2022-0609, in February. According to TAG, North Korean-backed state hackers exploited the CVE-2022-0609 vulnerability weeks before the February patch. The earliest attacks that actively exploited the weakness were found on January 4, 2022.
2022 hasn’t just been about security updates for Chrome, though. Google in February updated the internet browser’s logo for the first time since 2014, with the new logo debuting in version 100 last month.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

