iOS, OS X Keychain Flaw Exposes Data from Millions of Devices
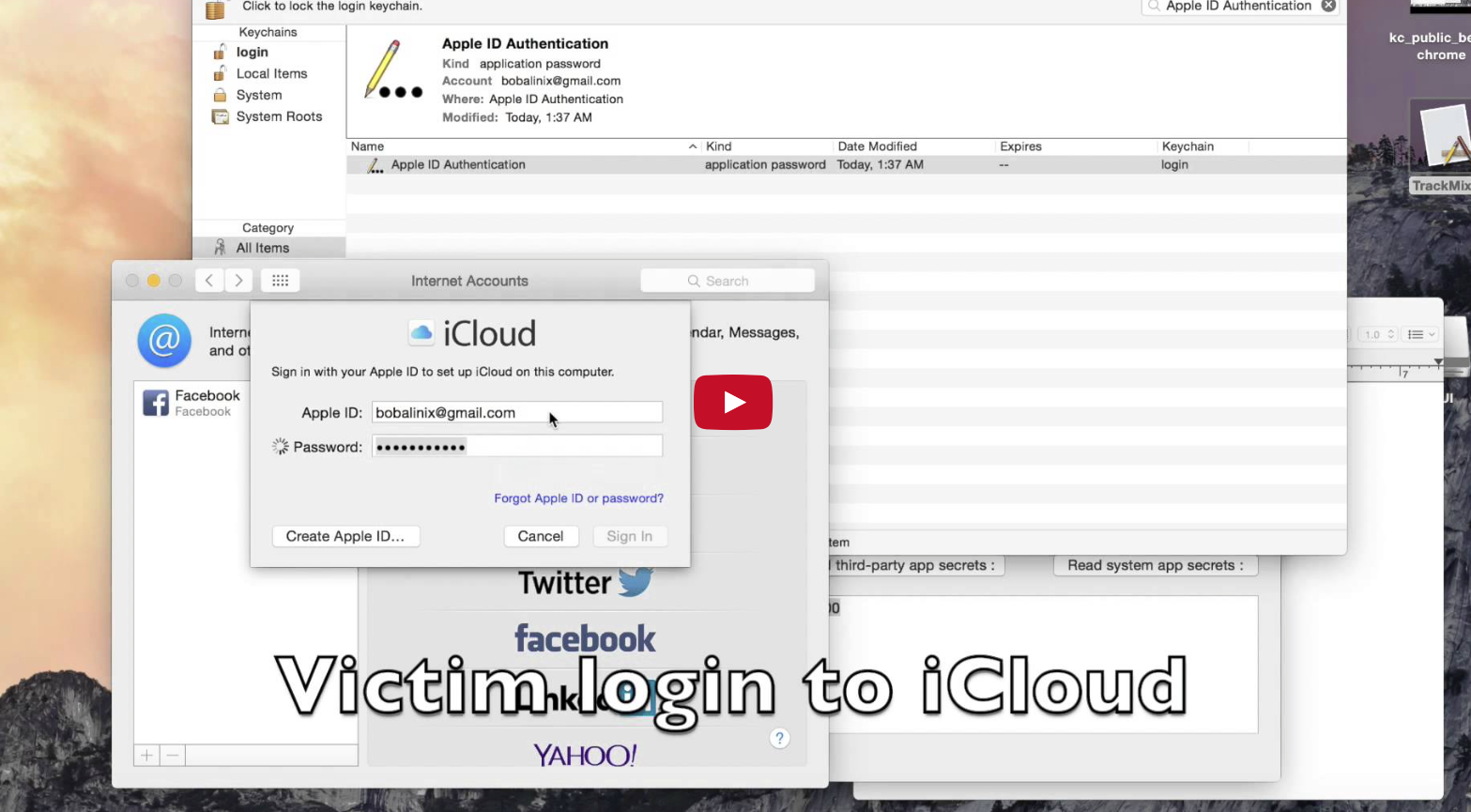
Six months after first notifying Apple about a serious zero-day security hole found both in iOS and OS X, six researchers from Indiana University, Georgia Tech, and Peking University have decided to break the silence: Apple left millions of users vulnerable to unauthorized access to sensitive data such as iCloud passwords, authentication tokens, etc.
The comprehensive report highlighting the security weaknesses of both operating systems, comes after Apple failed to patch the flaws with the latest software updates. In the research paper, entitled “Unauthorized Cross-App Resource Access on Mac OS X and iOS”, we can see the details of how the researchers managed to circumvent Apple’s security measures.
Speaking with The Register, Lead researcher Luyi Xing said the team complied with Apple’s request of withholding this information from the public for six months. Yet, as of writing this article, the security flaw still exists on both platforms, with devastating consequences, they say.
As detailed by Xing, the researchers completely cracked the keychain service and sandbox containers on OS X, identifying new weaknesses within the inter-app and inter-system communication mechanism on OS X and iOS. This allows knowledgeable hackers to upload malicious apps to the App Store (both iOS and Mac App Store) that could steal confidential data.
Our study brings to light a series of unexpected, security-critical aws that can be exploited to circumvent Apple’s isolation protection and its App Store’s security vetting. The consequences of such attacks are devastating, leading to complete disclosure of the most sensitive user information (e.g., passwords) to a malicious app even when it is sandboxed.
Such findings, which we believe are just a tip of the iceberg, will certainly inspire the follow-up research on other XARA hazards across platforms. Most importantly, the new understanding about the fundamental cause of the problem is invaluable to the development of better app isolation protection for future OSes.
You can read the full report by following this link. We assumed Apple moved faster to protect its users. Samsung asked for a year to fix a serious security hole, and Apple hasn’t done anything (visible) during the past six months to fix the issue. We don’t have information about iOS 9 and OS X El Capitan, though, so let’s hope Apple will fix it by this fall when they hit the public.