
Evasi0n Downloaded Over 1.7 Million Times
I think the new trend on Twitter could be “Monday is Funday”, as evasi0n reached the public yesterday, after long months of waiting. Some of us who spent time hacking their iDevices yesterday had to wait until they could install any of available jailbreak tweaks, because Cydia was overcrowded. Why? Jay Freeman Cydia’s administrator has the answer.
As Freeman points out, in its first six hours of availability, evasi0n had already been used at least 800,000 times, but that was just the beginning. The heavy traffic of jailbreakers around the globe knocked his server offline a couple times yesterday, and by this morning evasi0n had been used by 1.7 million users.
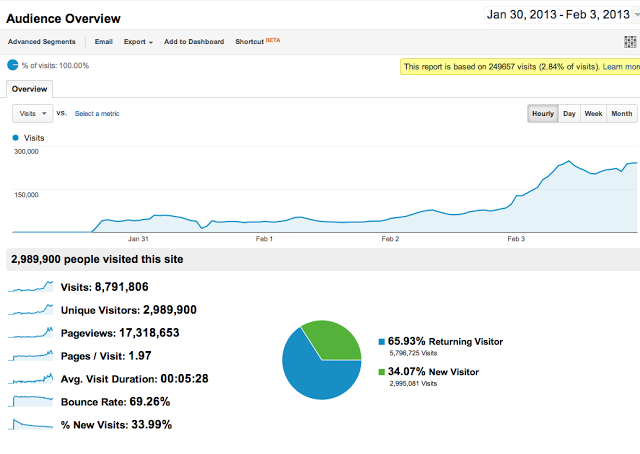
An interesting addition comes from Pod2g, who posted a Google Analytics screenshot showing that the evasi0n website was visited by nearly 3 million unique visitors before the tool was released.
Speaking with Forbes, David Wang, one of the Evad3rs, said the new untethered jailbreak tool takes advantage of at least five distinct new bugs in iOS code, despite Apple having done a good job in making iOS 6 more secure than ever. Here is how the final stage of the hack works.
iOS has yet another safeguard to prevent hackers from altering memory in the operating system kernel: Address Space Layout Randomization, or ASLR. That defensive trick moves the location of device’s code in its flash memory a certain, random distance every time it boots up to stymie anyone who would write over a particular part of the code. But evasi0n uses a memory allocation trick to locate one spot in memory that’s harder to hide in ARM-chip-based devices, known as the ARM exception vector. That part of the kernel handles application crashes, reporting on where in memory they happened. So evasi0n simulates a crash and checks the ARM exception vector to see where the crash occurred, providing just enough information to map out the rest of the kernel in the device’s memory.
Once it’s beaten ASLR, the jailbreak uses one final bug in iOS’s USB interface that passes an address in the kernel’s memory to a program and “naively expects the user to pass it back unmolested,” according to Wang. That allows evasi0n to write to any part of the kernel it wants. The first place it writes is to the part of the kernel that restricts changes to its code–the hacker equivalent of wishing for more wishes. ”Once you get into the kernel, no security matters any more,” says Wang. “Then we win.”
Have you hacked your iDevice running iOS 6.1? If not, you can do it right now, following our jailbreak tutorial.

