Apple Updates OS X Malware Definitions To Protect Users Against ‘iWorm’
Russian security researcher Doctor Web recently discovered that more than 17,000 Macs around the world have been infected with a new OS X malware called “iWorm”.
The malware known as “Mac.BackDoor.iWorm,” which at one point used Reddit to collect user data, is able to gather information on you Mac as well as control your system (in a limited fashion).
Once the malware determines that your Mac is vulnerable, iWorm attempts to establish a link to a command server and then waits for an inbound connection. Once iWorm is installed on a users system it generates a file and unlocks a port on the infected computer, allowing the infected computer (also known as a “Botnet”) to communicate with the command server.
After the connection to the remote command server is established, the attacker can initiate commands to the infected computer. Botnets are most commonly used in denial-of-service attacks, which flood a web server with traffic until they crash.
The new malware found on OS X can also be used to collect and transmit user information, download files, perform GET queries, and perform several other backdoor operations.
The Reddit thread that was used by the attackers to communicate has been shutdown. However, it is very likely that the hackers have placed a server list elsewhere.
There is a flaw in the piece of malware which allows users to detect if their Mac is infected. Since iWorm extracts into a folder on OS X, user can check if that folder exists to determine if they are infected.
From the OS X Finder menu navigate to “Go > Go to Folder” and type in “/Library/Application Support/JavaW”. If your Mac cannot find the folder, your computer is clear. However, if the folder is found, your Mac is infected and users are encouraged to format and reinstall OS X.
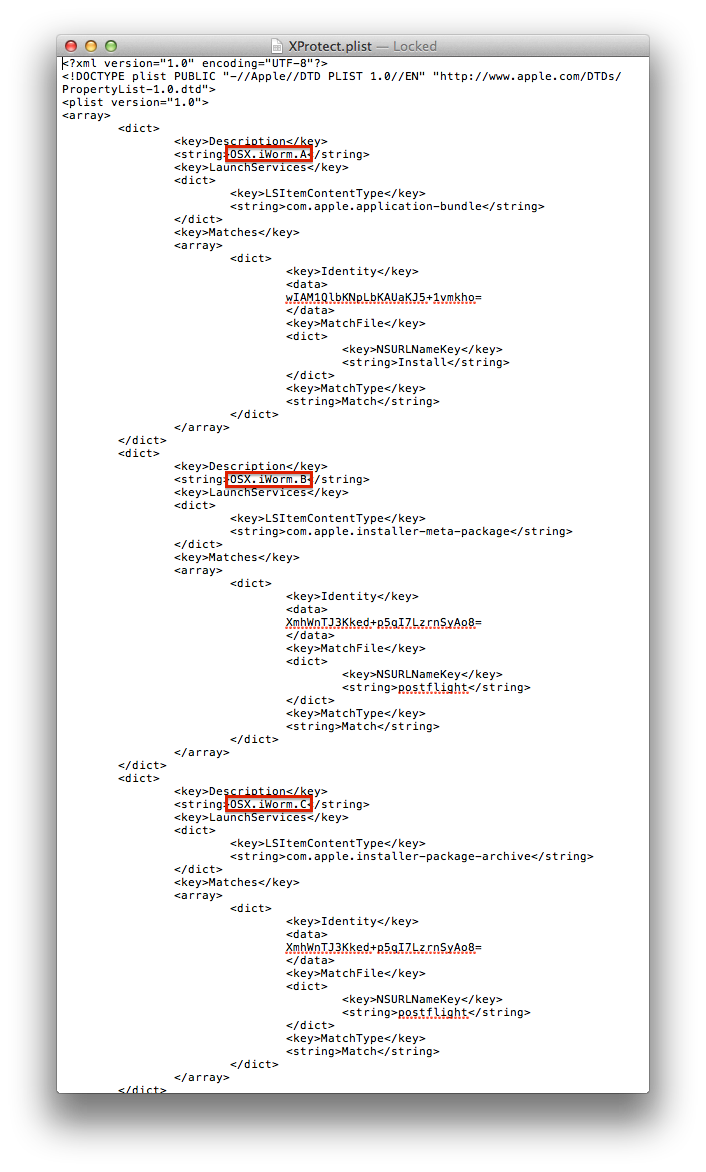
According to a report from MacRumors, Apple has updated its “Xprotect” malware detection system to recognize three different versions of the iWorm malware and prevent installation. All three dictionary definitions in the “Xprotect.plist” file can be seen in the image above. The company will continue to update this file if more variations of the malware is found.