
FBI Contractors Find Ways to Break WhatsApp’s Improved iCloud Encryption
Last year, WhatsApp quietly improved the security of its iCloud backups with a unique encryption key created by the app, instead of relying on the iCloud Drive alone to protect customer data. This is on top of the end-to-end encryption rolled out across one billion WhatsApp users. Forbes however learned about this encryption only last week after an FBI contractor from Russian claimed to have found a way to break into the added encryption.
According to a Russian supplier of mobile and cloud hacking tools, Oxygen Forensics, their latest tools have added a feature that allows the company to circumvent the enhanced WhatsApp encryption for its iCloud backups. Vladimir Katalov, CEO of rival forensics firm and another Russian business, Elcomsoft, has also detailed how the update worked and what Oxygen was doing to circumvent the encryption.
He explained that while Oxygen isn’t wrong about its updated tools, they will only work in “a very specific scenario”.
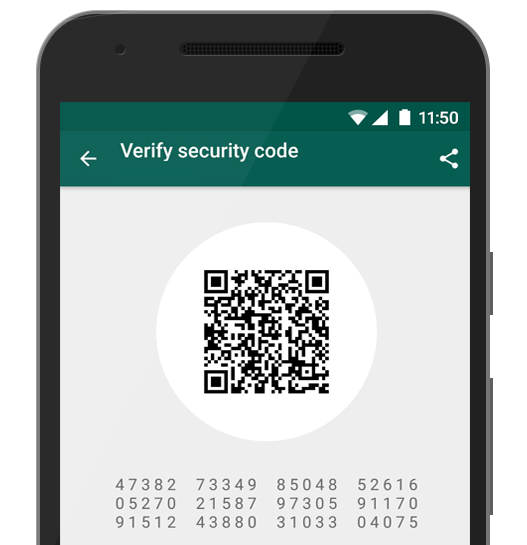
As explained by Katalov, when the user opts to upload their WhatsApp data to the iCloud Drive, and they’ve entered a texted verification code sent by the Facebook-owned firm, a unique encryption key is generated. That key is then used to encrypt the data uploaded to the iCloud Drive. Forensic tools can download that data but in order to decrypt it on any device other than the original iPhone, the key is now needed, and that can be obtained only by passing the verification process again.
So what Oxygen does is download data backed up by WhatsApp, and they then require a SIM-card with the same number as the user so they can receive the verification code. They can then generate the key and decrypt downloaded data.
Although Oxygen seems to have found a way around the boosted protection added by WhatsApp, it still needs the Apple ID and password or some other access to the iCloud, and the user’s SIM card or phone.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

