
iPhone Hack Prices Act as Apple Security Barometer
Apple seems to like iPhone hack prices being high – just think about the roughly $1 million the FBI paid for a zero-day vulnerability to access the San Bernardino shooter’s iPhone 5c. In fact, Apple head of security engineering and architecture Ivan Krstic has used such reports as an “indirect metric” to evaluate how well the company is performing (via Tech Insider).
Krstic admitted that there is a black market for software vulnerabilities, and sometimes prices paid for a zero-day vulnerability become known. The usual prices for such vulnerabilities “are tens of thousands of dollars, sometimes $100,000”, he says.
But that’s the price you pay for a Microsoft Windows or Android bug. If you are looking for an iPhone bug, you have to think in terms of a bigger sum – much bigger. Krstic pointed to two reports: A New York Times report puts the price of an iPhone hack at half a million, and a Forbes article says the going rate for an iOS vulnerability is $1 million.
“Take that with a grain of salt, but it’s a fascinating number to think about,” Krstic said. “What you’re seeing now is the result of a decade of our best work in protecting our users.”
In April, Apple said that it has “the most effective security organization in the world,” and during Krstic’s talk, he bragged that the iPhone hasn’t had a virus or malware problem at scale over the past nine years.
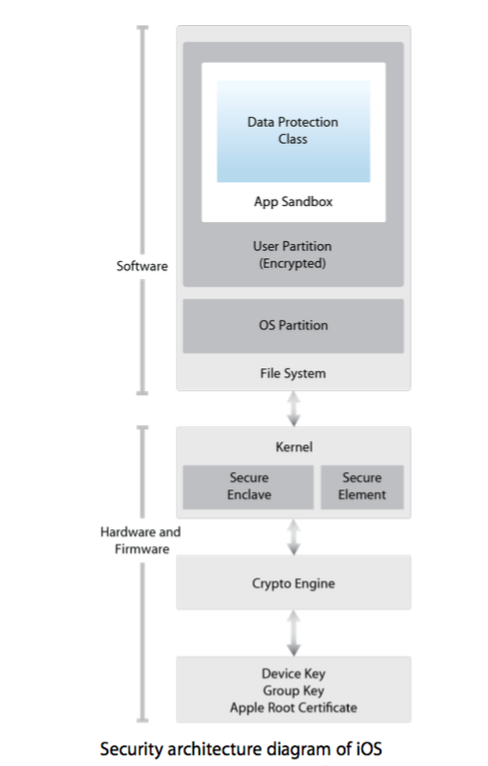
There are ways to squash the black market for such vulnerabilities, such as offering a “bug bounty” program. Apple has decided to skip that, and instead, with iOS 10, it has opted for leaving the operating system’s heart, the kernel, unencrypted, as it doesn’t contain any user info. Security researchers say this is how Apple aims to address the black market for iOS vulnerabilities, as it has made it much easier to identify a bug and report it to the company. Apple always publicly credits developers and security researchers if the bug is confirmed and gets fixed.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

