
Security Backdoors and Surveillance Mechanisms Reportedly Found in iOS Devices [u]
Security researcher and iOS forensics expert Jonathan Zdziarski has published a paper and hosted a talk at HOPE/X about identifying backdoors, attack points, and surveillance mechanisms in iOS devices.
Zdziarski has found that there are several services in iOS that reportedly facilitate organizations like the NSA. The services do not require the user to be in developer mode for them to work, therefore they are available on every iOS device.
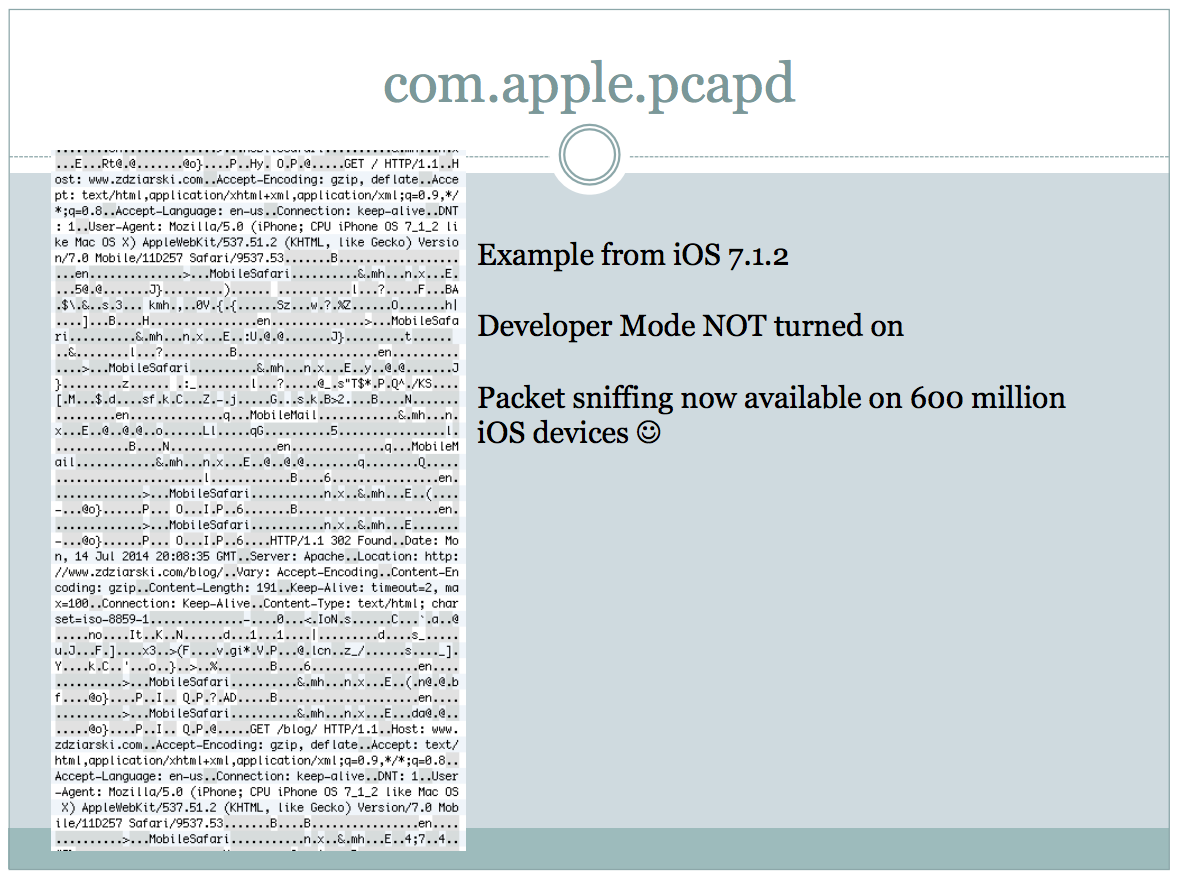
For example, one of these services that Zdziarski points out in his presentation slides is a packet sniffer called “com.apple.pcapd”. The service “dumps network traffic and HTTP request/response data traveling into and out of the device” and can be targeted via WiFi for remote monitoring.
The packet sniffer is active on every iOS device and can be run without any visual indication to the user. Here is a slide which shows a snippet of data from the packet sniffer:
Over the past several years, Apple has continuously promoted user security and privacy in iOS. However, according to findings by Zdziarski, he believes this does not seem to be the case, as his research claims the company is making it even easier to get your data.
Zdziarski’s journal paper can be purchased for a small fee or you can read through his presentation slides from his HOPE/X talk for free. For anyone interested in the security mechanisms found in iOS, the presentation slides are an interesting read.
Contrary to this research, Apple has long stated it does not work with the NSA and their iOS devices are secure, as reiterated by CEO Tim Cook.
[via Twitter]
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


Link bait! I’m guessing iOS is still far more secure than Windows and Android.
Unless you work for Apple, Google and Microsoft you can never say for certain which is more secure. The researcher above found proof that iOS is collecting your information and data about your activity.
You don’t have to work for Google to be sure your Android is secure, all you have to do is installing AOSP-based ROM, one you have the sources for.
And no, iOS s not more secure than Android.
Wow….. Windows Phone! Or get an Android device and encrypt the device. One other reason I don’t want Apple devices….. that and the horrid music sound quality.
You should be more concerned with Google and your android device. Biggest spies out there.
Try changing your ear/headphones, mp3/ogg quality maybe? The device has nothing to do with the quality of the music.
The device have EVERYTHING to do with the quality of music, it’s called digital signal processing, and more precisely here, it’s the digital-to-analog conversion which suck on most Apple embedded devices. If the device don’t produce good signals, you can play the best quality audio file, on the best quality headphones, the quality will still be mediocre.
I can’t believe how people can be so ignorant and yet think they know everything.
No Kidding! How Bizarre ! marc
This article is misleading. The pcap packet capture library is very common (standard) on Unix-like systems like iOS. Its presence doesn’t mean it’s being used to spy on you unless there’s an app running on your phone that is actively using it. There are billions of Unix-like and Windows computers with pcap installed.